In this article, we will show how you can download and use Desktop Google Drive for Windows, Mac & Linux. When we talk about Google Drive it makes sense a lot, Because this drive makes it easy to access and use your cloud storage files. It is very popular, useful, and also compatible with Google online tools. We should mention that if you want to use this drive, you should have a Google account and if you desire to have it, then the best way is to install it on your desktop and mount it to access. Google Drive consolidates with Google’s other services and systems like Chrome, Gmail, Google Docs, YouTube, Google+, and so on.
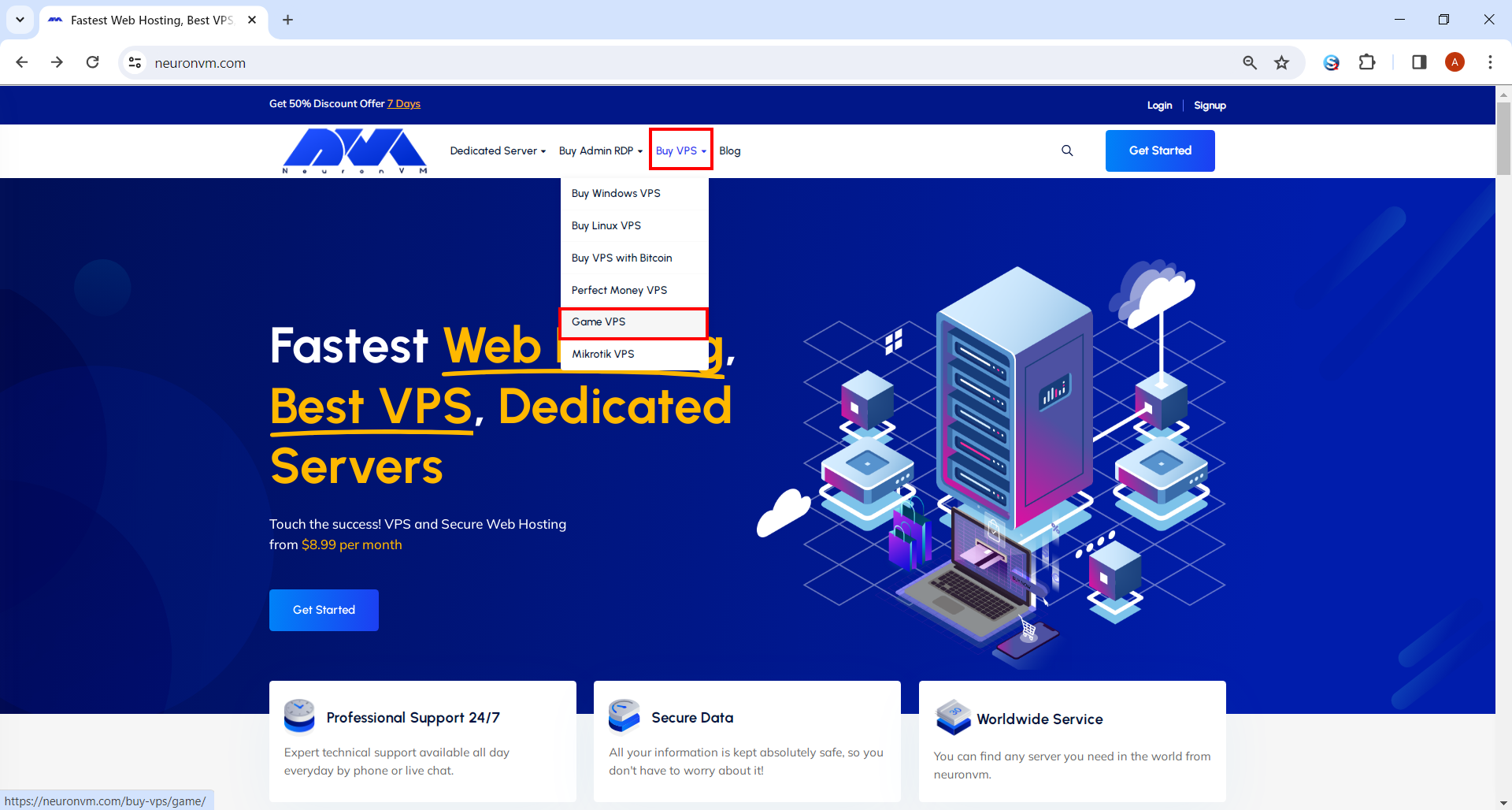
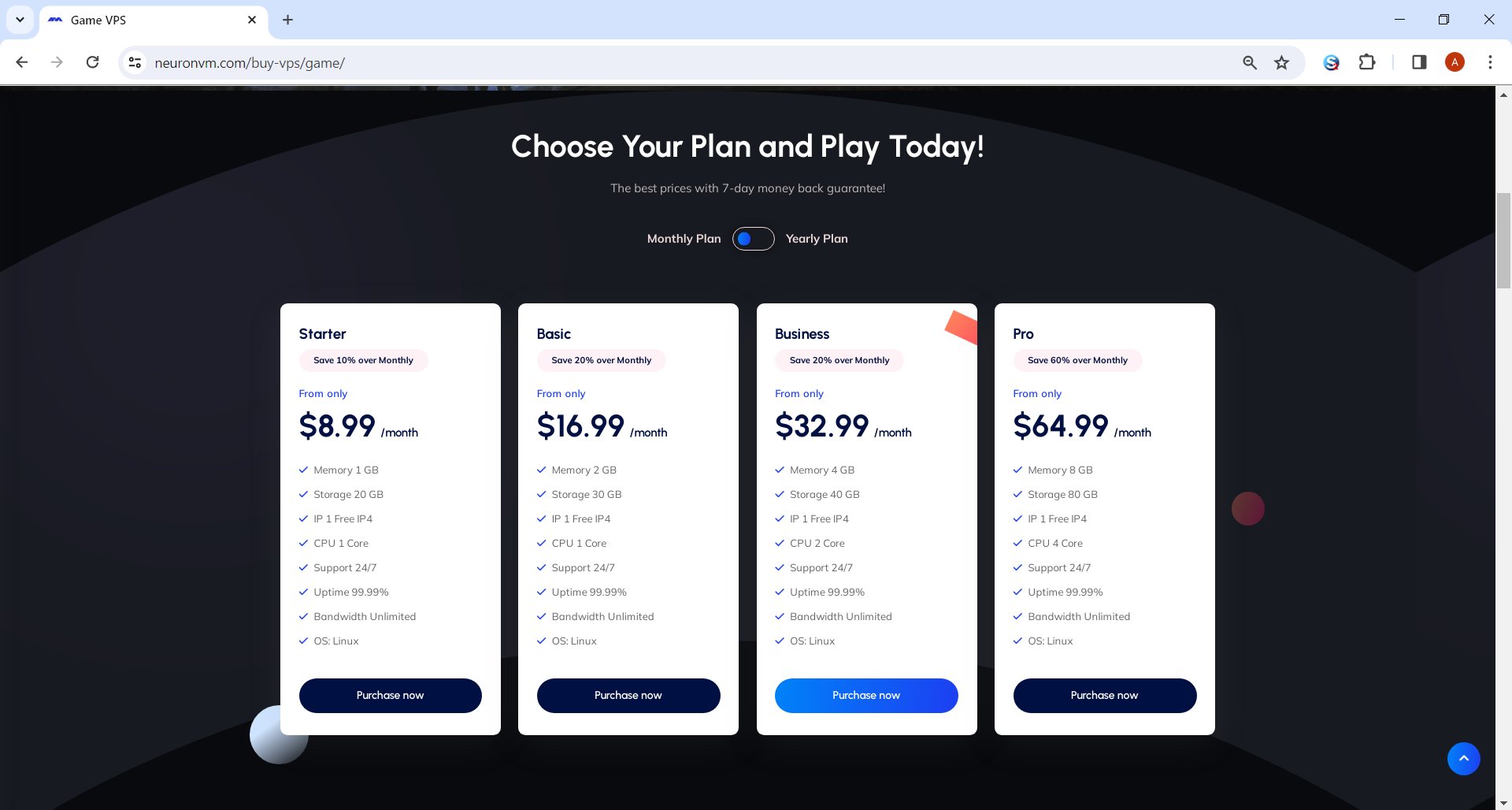
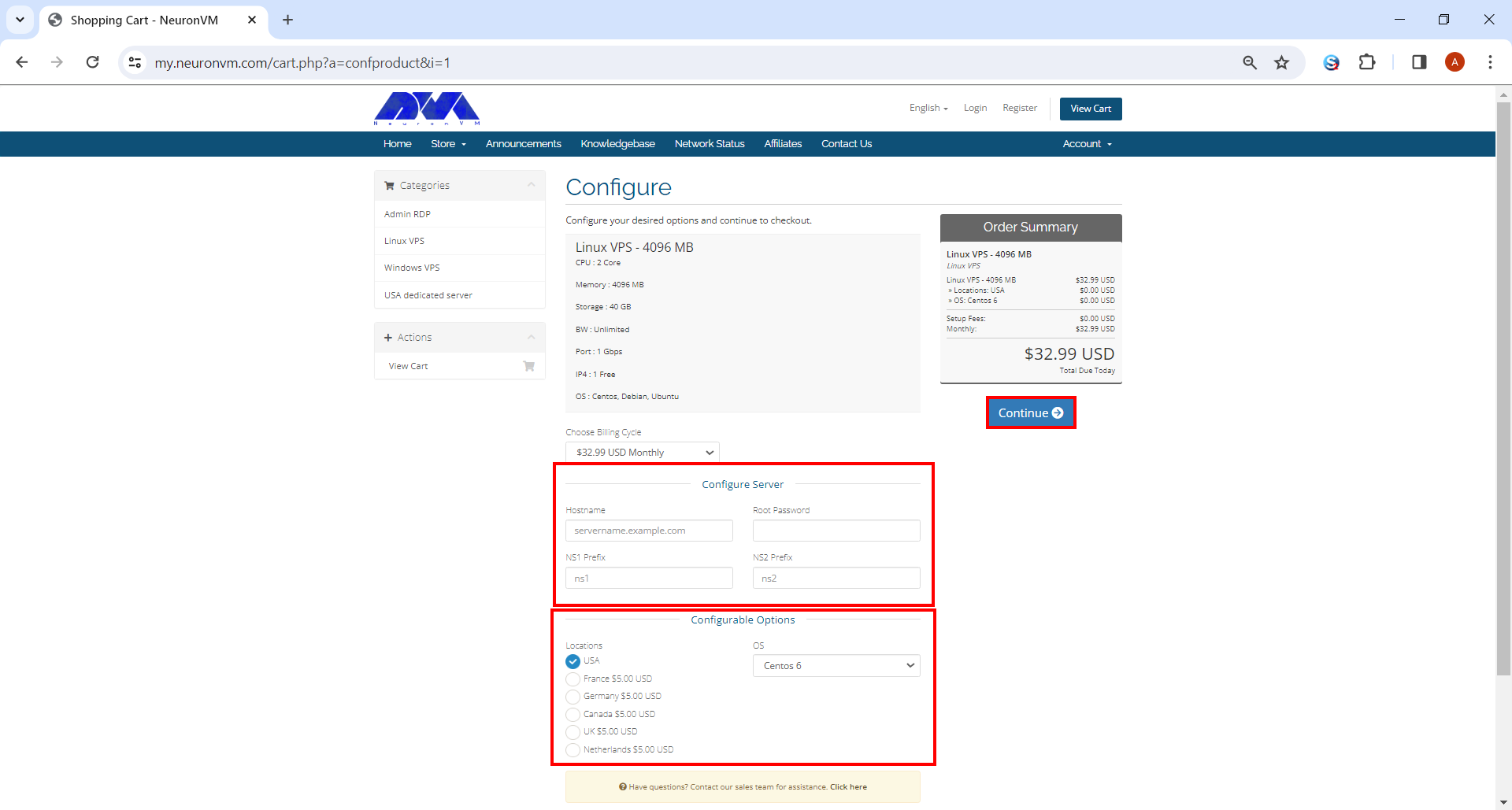
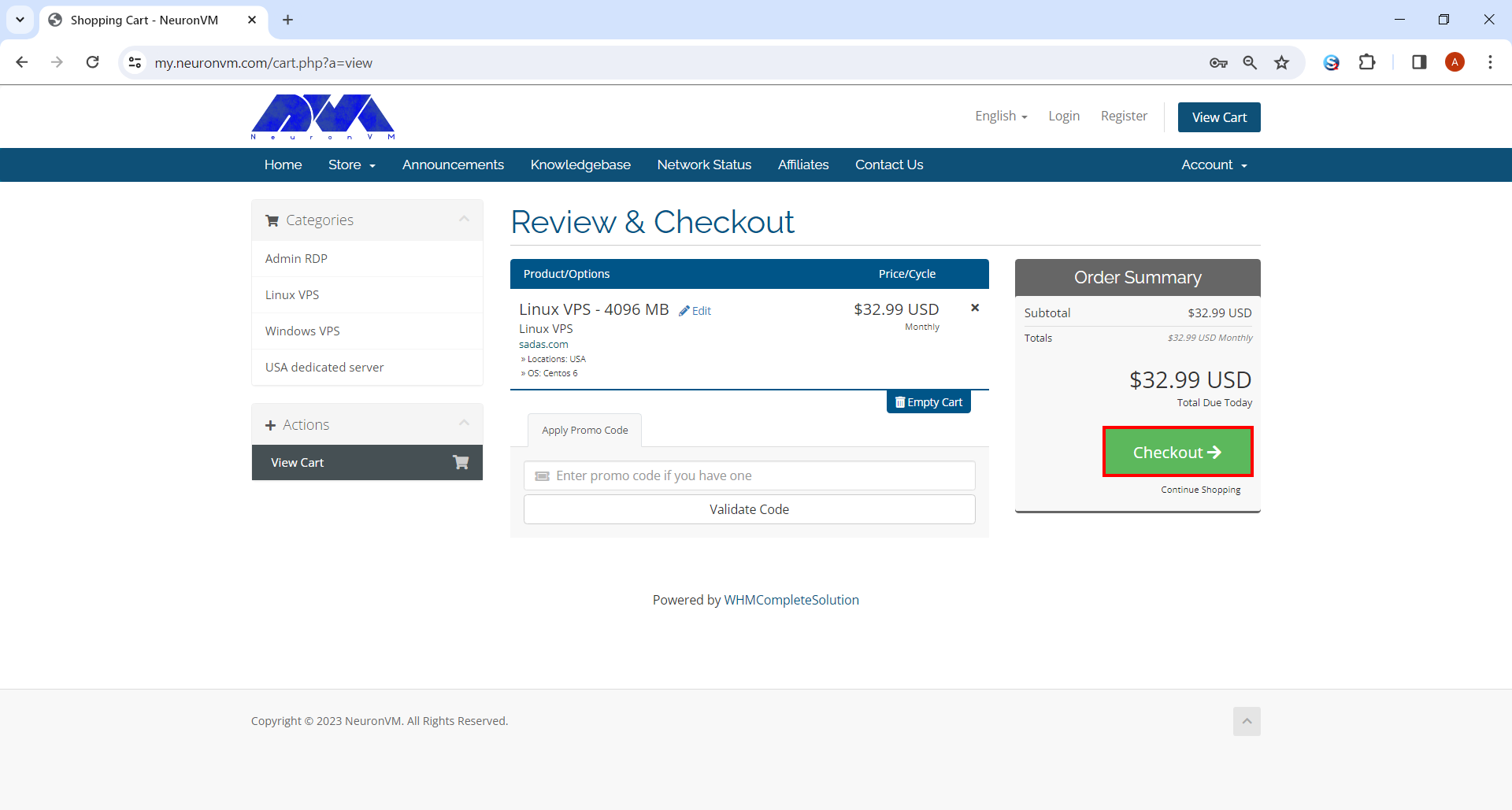
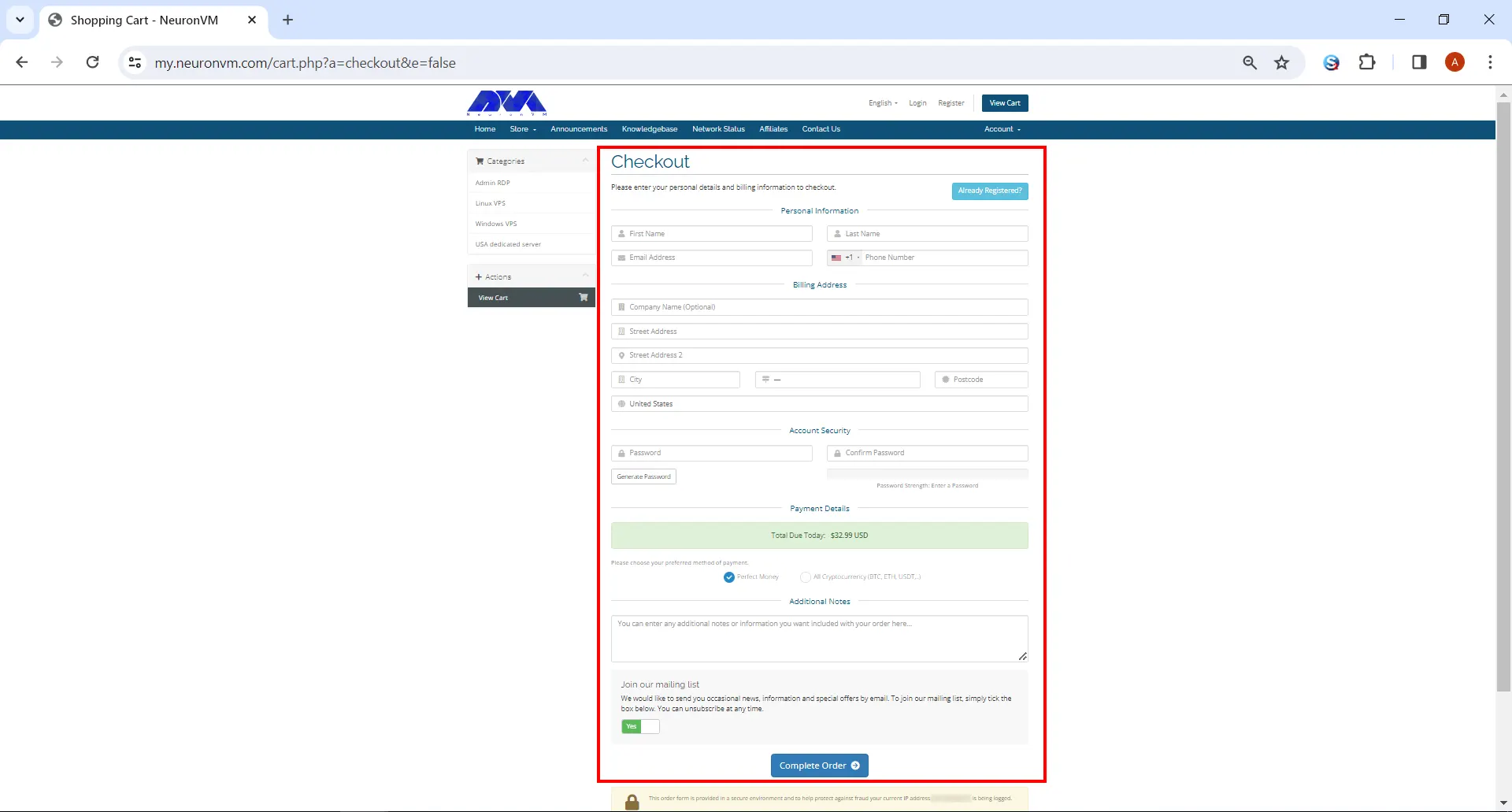
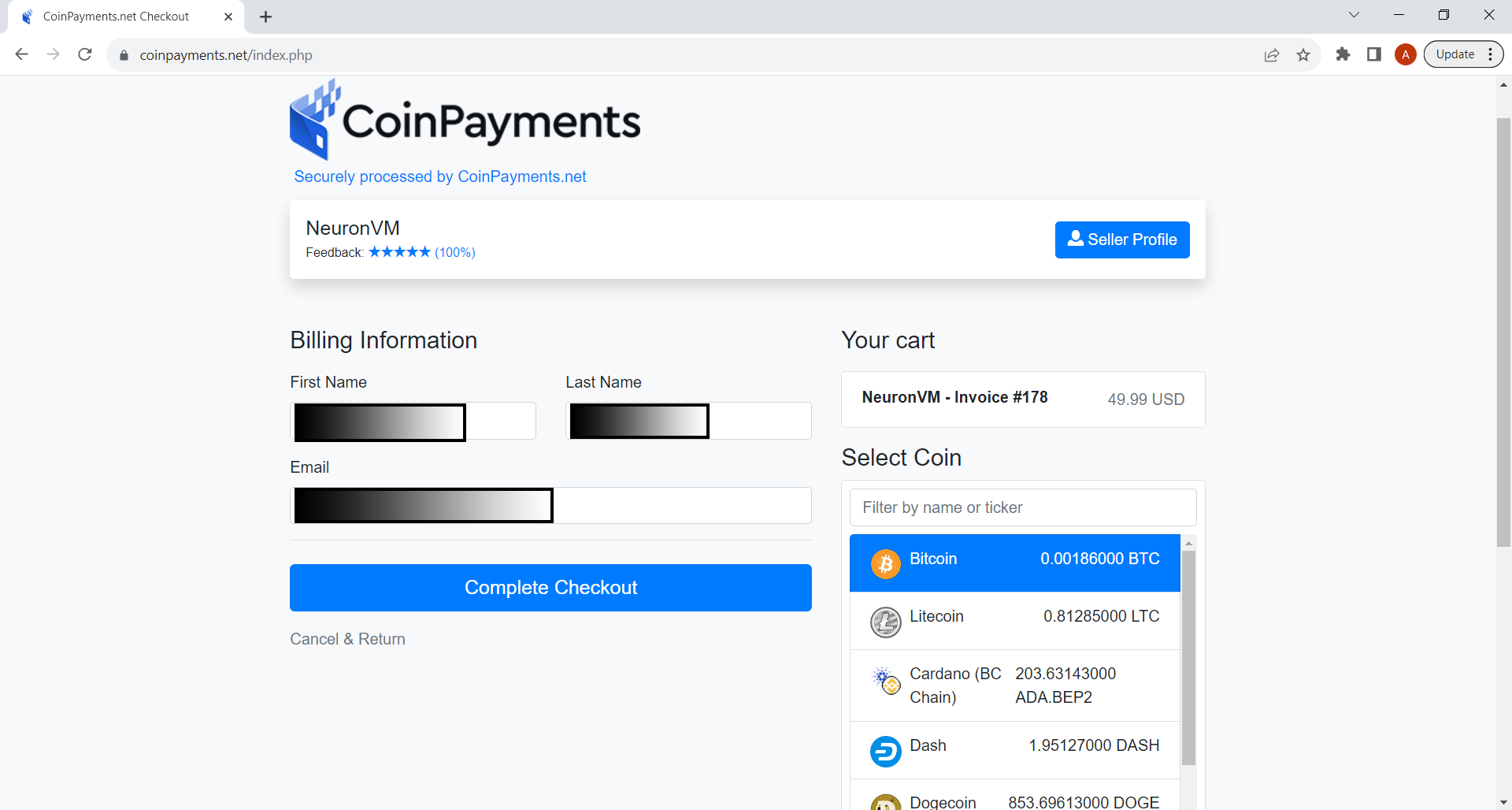
If you need to use a Windows VPS or Linux VPS server, we suggest you visit our website plans, which are offered with a wide variety and location of your choice.
Google Drive Features
Now let’s analyze some main features of Google Drive:
– Capability of storing files and folders and serving a backup solution
– Integration of Google Office apps
– Include different apps and icons like Google Docs, Google Sheets, Google Forms, and so on
– Allow to share files and invite others to view, edit, and download them
– Accessibility of files from any smartphone, tablet, or computer online or offline
– Possibility of comprehensive search
– Saving files safely and protecting them with an AES256 or AES128 encryption
How to Download and Use Google Drive on Windows / Mac
Now that you’re familiar with Google Drive, let’s see how we can install it on your desktop for Windows or MacOS. Actually, you can easily do the installation process and it is entirely free for you, so follow our instructions and enjoy your application.
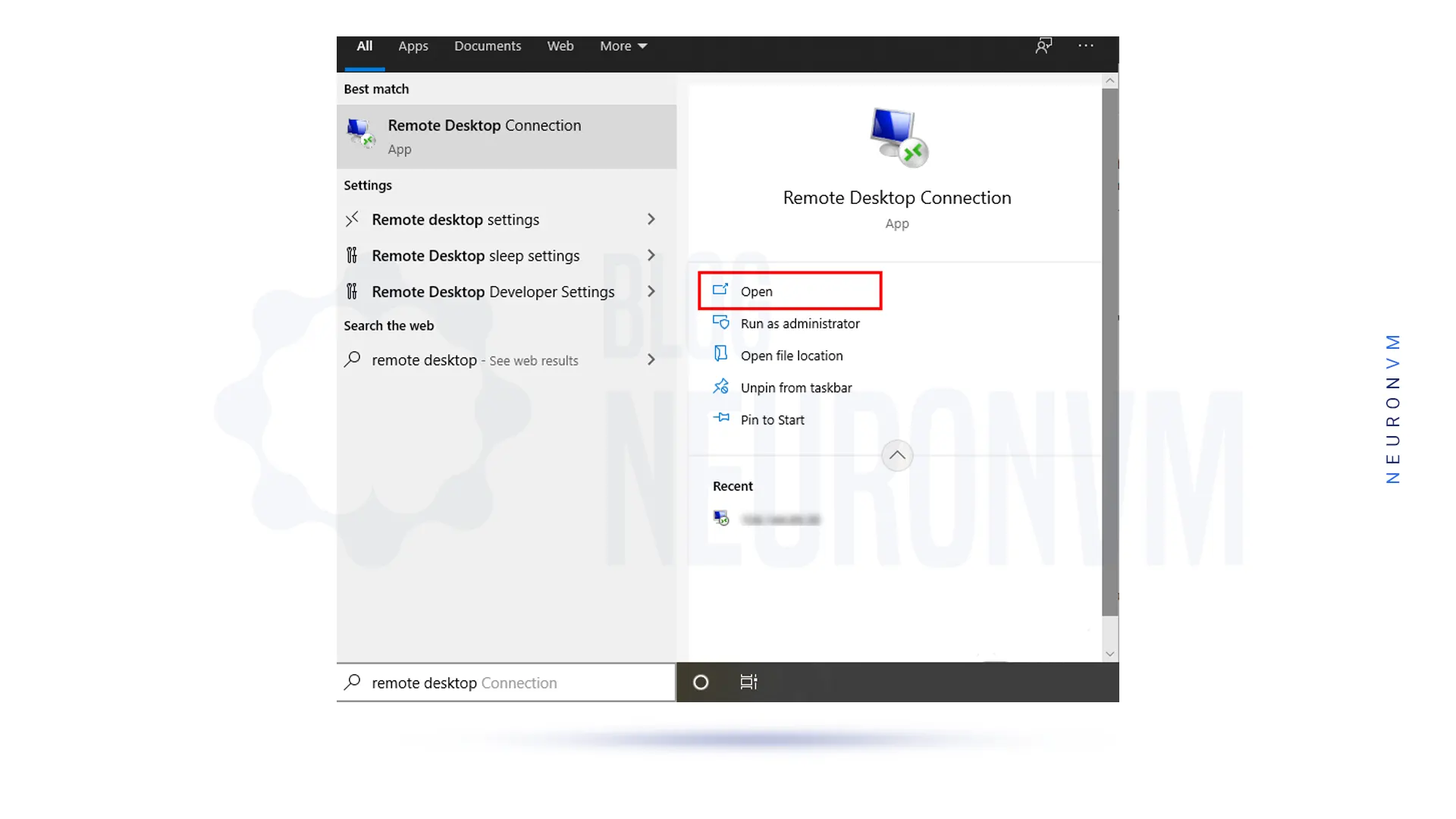
Navigate to the Google Drive download page and select the option to download Drive for Desktop. As the website is intelligent, it can automatically recognize your operating system and will download the appropriate file type for you:
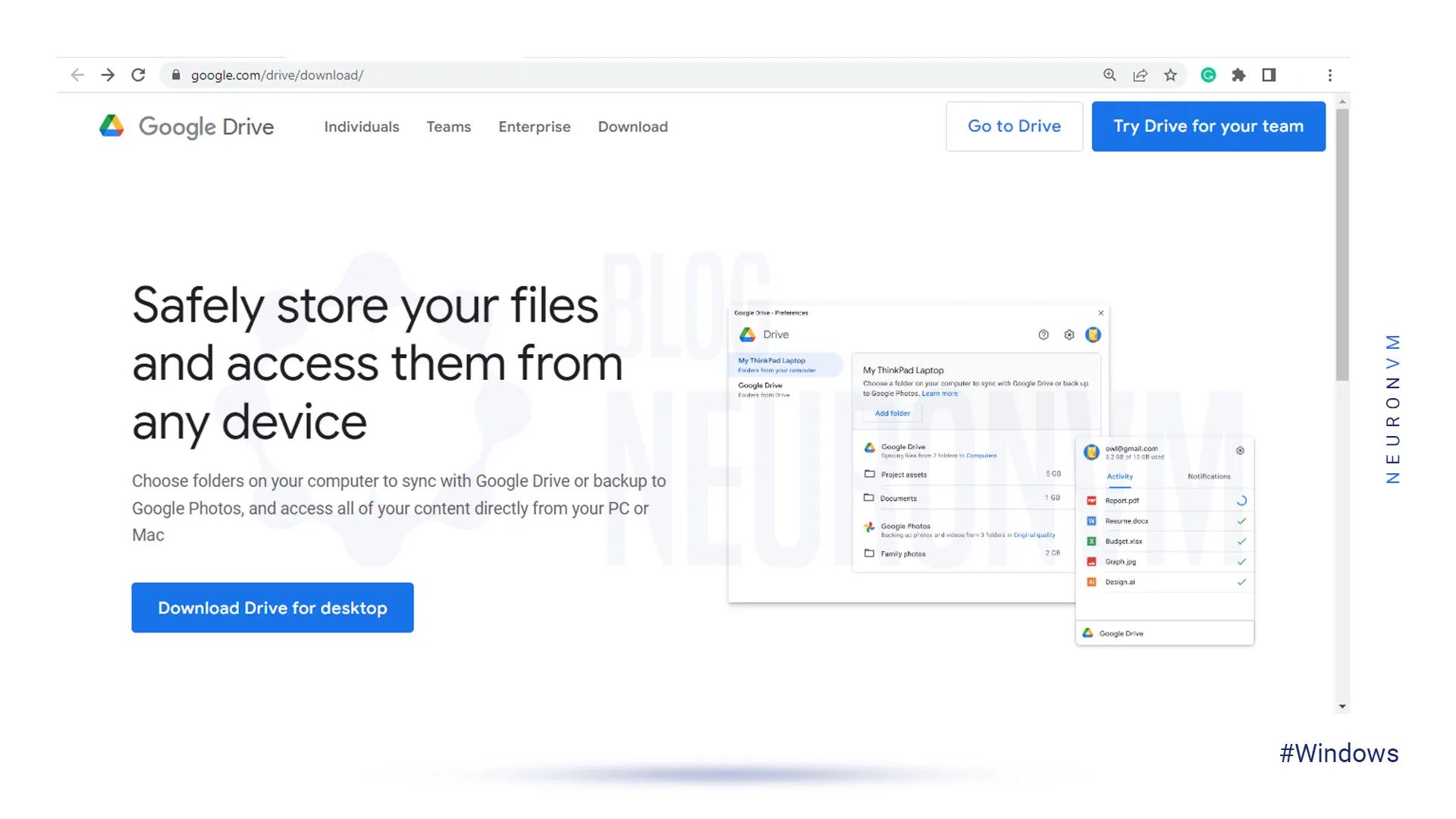
At this step, as soon as the window appears, select which folder you need to save the installation file and click the Save button.
For Windows, you should use Googledrivesetup.exe, and for Mac Googledrive.dmg file name.
Also, you can choose to open files automatically:
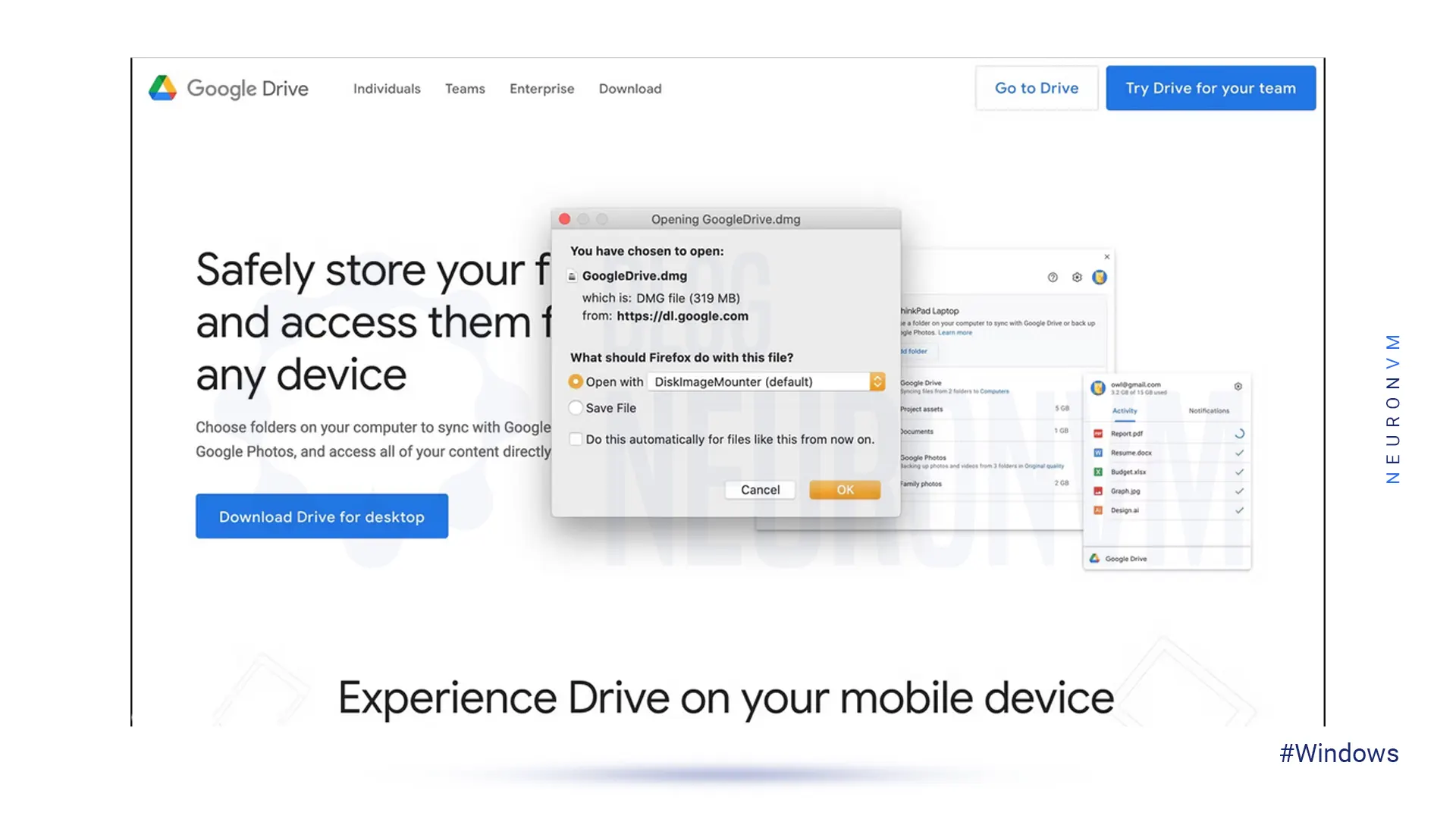
Now you can click the Install button to start the process.
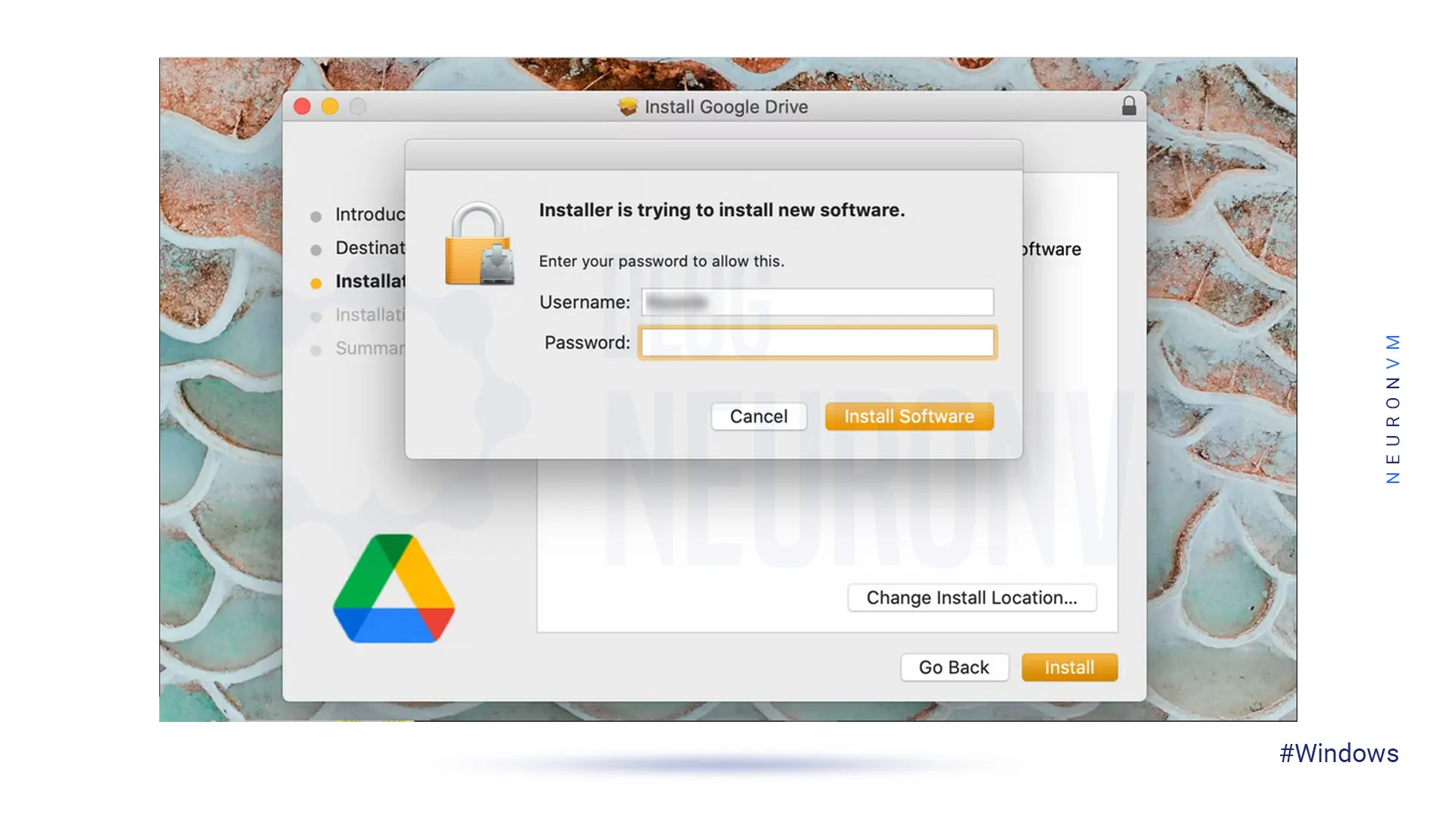
Note: on MacOS, an extra window will appear, requiring your Mac password to confirm the installation.
So enter the Password and click Install Software:
Wait for the installation to complete.
If your operating system is Windows, a new drive named Google Drive (G:) will be added to the desktop. But if it is MacOS the Drive icon will show up in the top menu bar:
![]()
In the last step, sign in to your Google account to complete your task. On Windows, you will be redirected to the browser and go to the login page. But on Mac, first of all, you should click the drive icon on the top menu bar and if you complete the installation successfully then you can log in to Google Drive.
How to Download and Use Google Drive on Linux
As you see, we can use Google Drive on Windows and Mac. But Google hasn’t released an official version for Linux. Don’t worry cause we can use other tools to fill the gap.
You should know that Google officially recommended using the Google Driver Website on Linux. But if you want to find it on your desktop, then follow our instructions:
First of all, you should know that Gnome supports Google Drive on its version 3.18 desktop environment. Also, the Ubuntu desktop includes Nautilus which is part of Gnome. You need to spend extra time getting the Google Drive integration. To start this process you should install the Gnome Control Center and Gnome Online accounts package. So open the terminal and use the command below:
sudo apt install gnome-control-center gnome-online-accounts
Enter your password and type “y” to install the software.
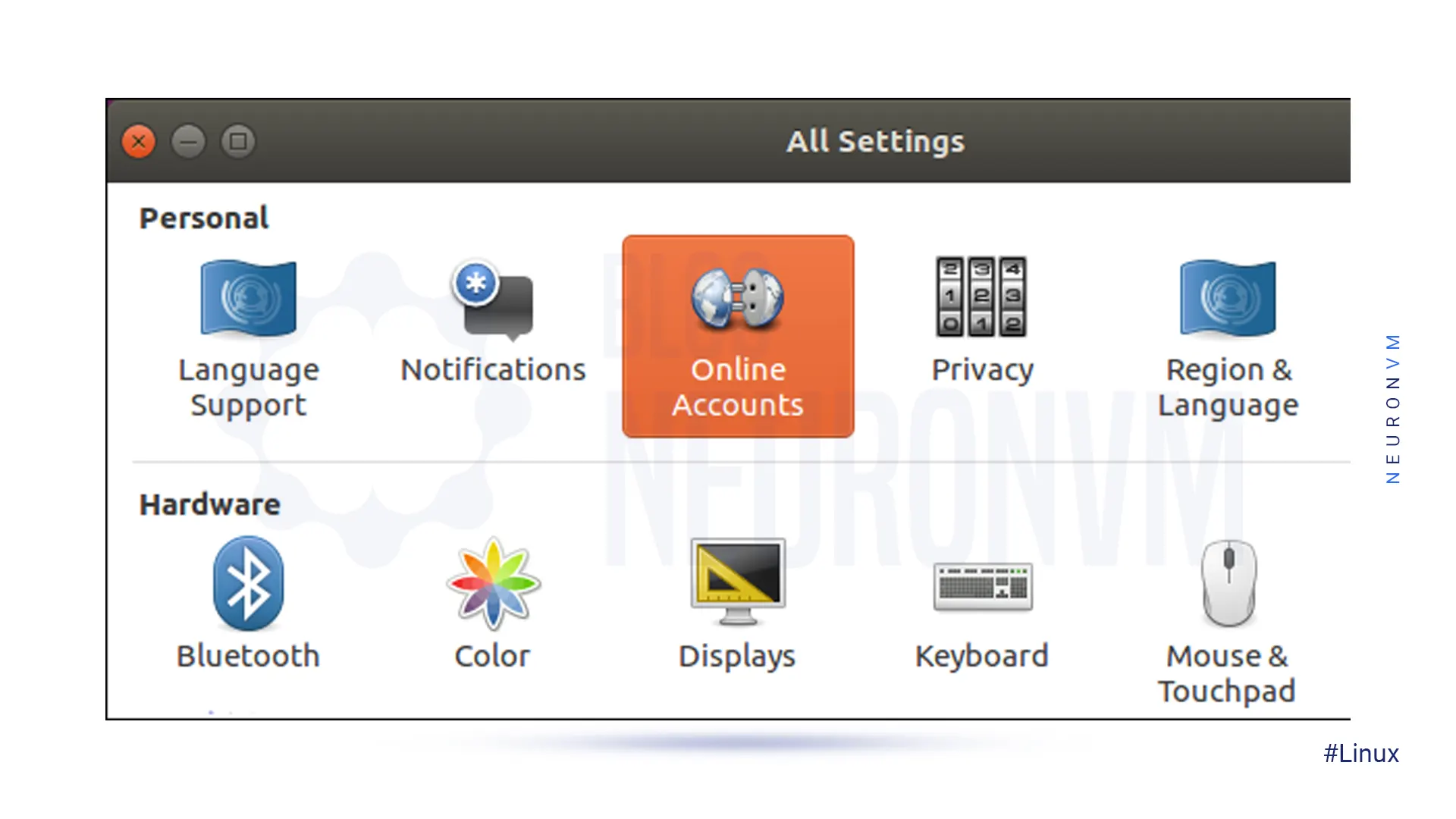
Then open the dashboard and search for “Gnome Control Center“. Navigate to the application settings:

At the window, click the “Online Accounts” icon in the Gnome Control Center window:
Now click the “add account” then select “Google” and sign into your Google account.
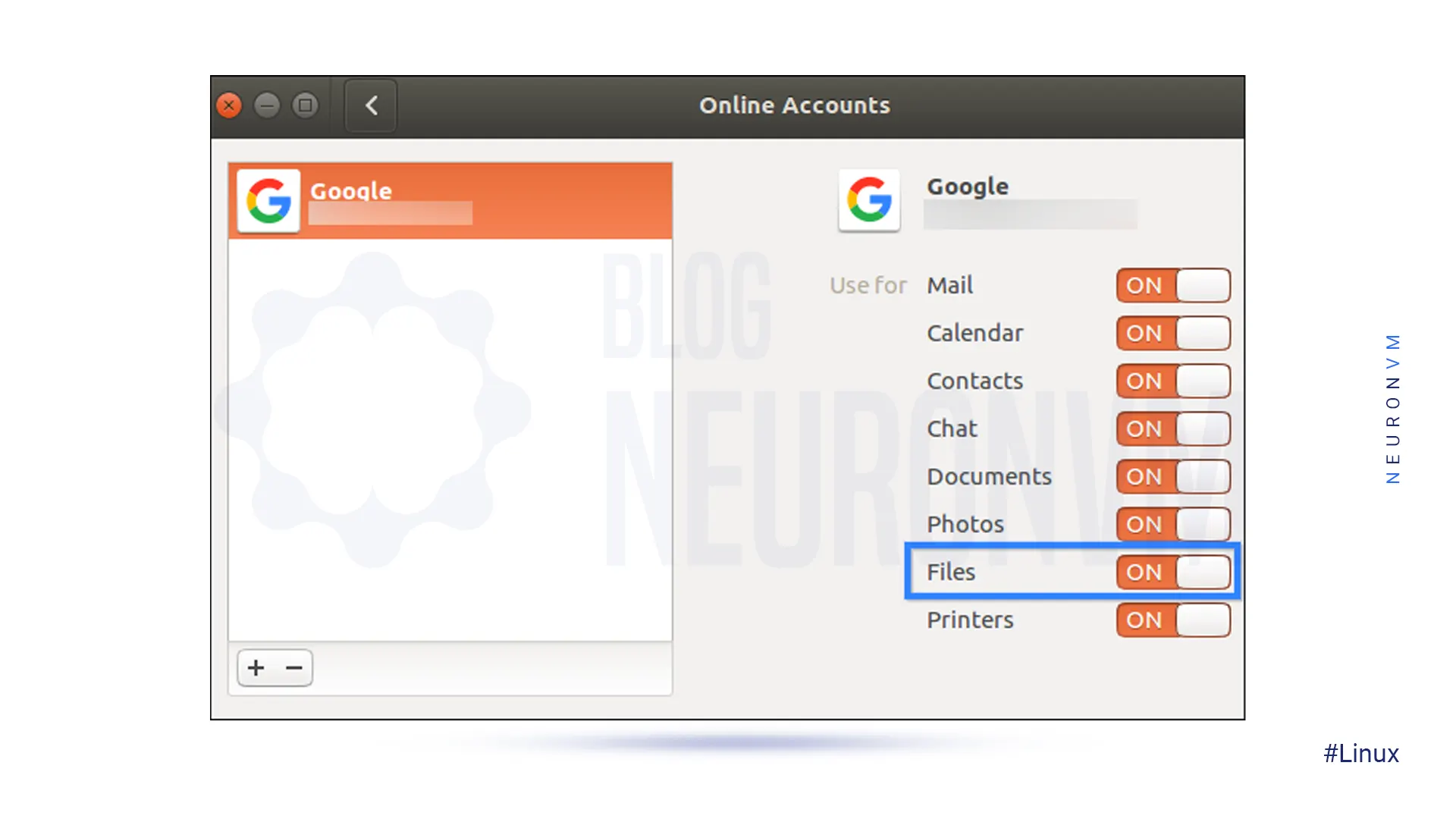
You can give access to your account and ensure that the files option is enabled:
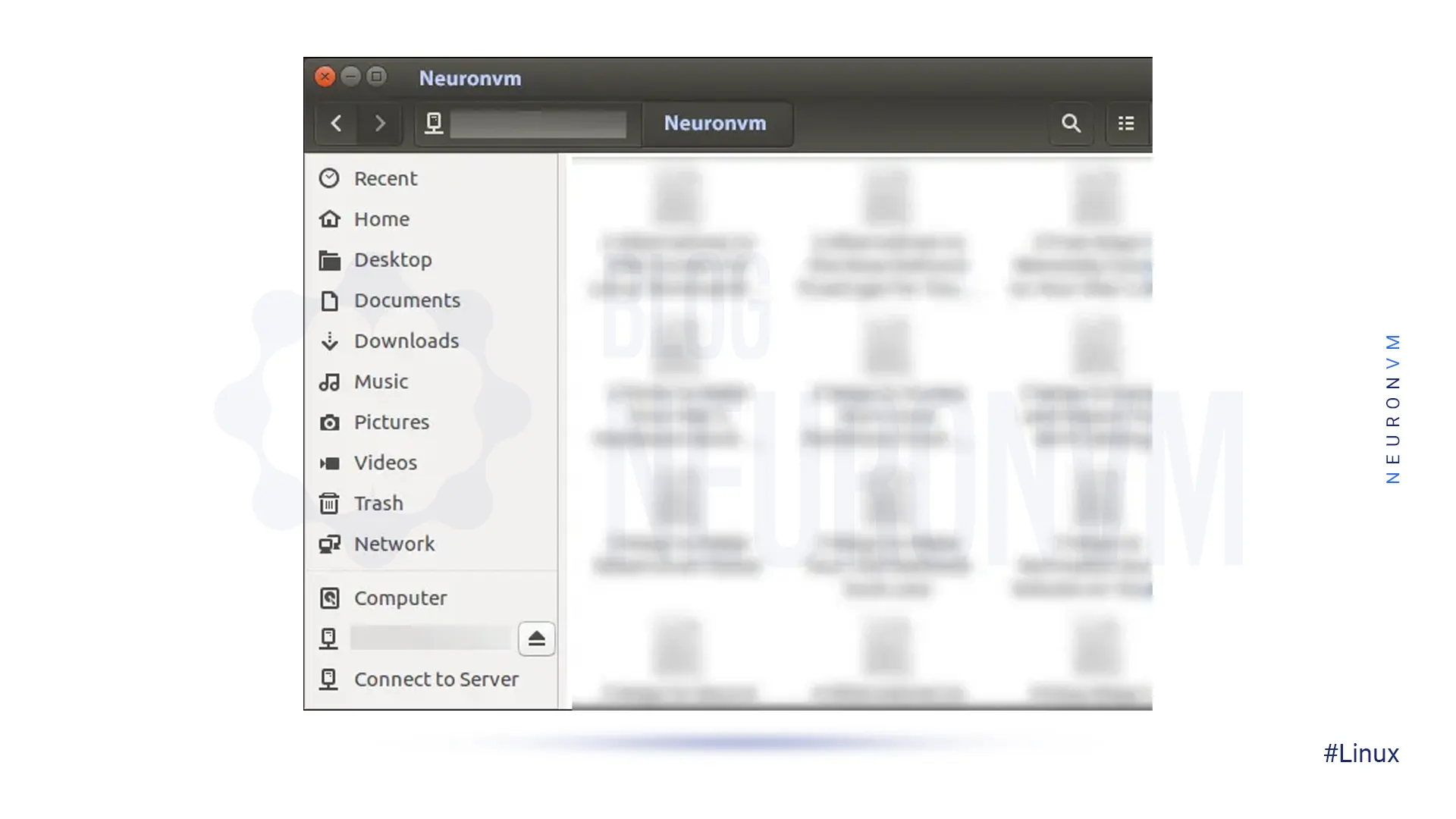
You can see the Google Account email address as an option in the sidebar at the file manager window.
Then click to view Google Drive files. You can browse, open, and save files, but files are not synced offline to the desktop. The modified copy will be automatically uploaded by the system:
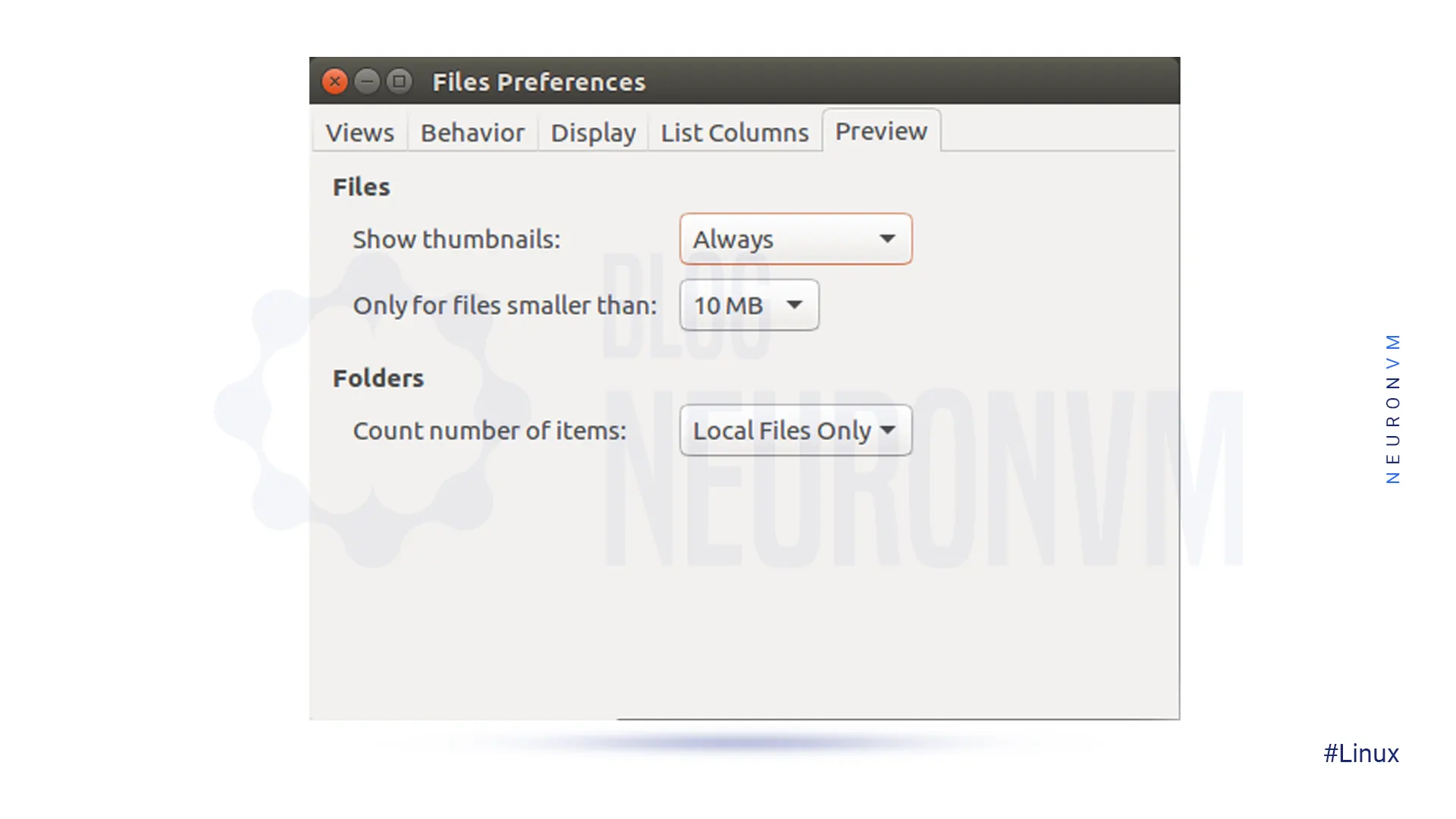
If you want to see the thumbnail preview, follow the pass below and then select “always“:
Edit >> Preferences >> Preview, click the “Show Thumbnail”
That’s it! Now you can use Google Drive on your desktop.
Conclusion
Ok, guys! We tried to guide you in learning how to download and use Google Drive on Windows, Mac, and Linux. Now you can easily download it on your operating system, and also manage and access your cloud storage files without any worries about security. We hope you enjoy this article and suggest that you read the interesting infographic post, Cloud Computing Structure.
FAQ
1) Is there any difference between Google Drive and Google Drive for Desktop?
The desktop version synchronizes and stores the content of Google Drive locally on the computer, but the first one streams all files and folders from the cloud.
2) What is the maximum storage for desktop Google Drive?
Actually, it comes with 15 GB storage, but if you upgrade it to Google One, your total storage increases to 100 GB or more.