If you are going to prevent malicious traffic or data coming from the Internet or other networks to your system, you need to know what a firewall is and how it works. Generally, a firewall is a device and network security mode that monitors incoming and outgoing network traffic and blocks or allows packets or information data to pass based on its security rules. In this post, with an Ultimate Guide to Protect Your System from Cyber Threats, we will tell you how to Secure Your AlmaLinux with Firewall.
Introduction to Firewall in AlmaLinux
A firewall is used to prevent sabotage and security of any system of this system. We must say that every system connected to the Internet needs its firewall to be active to prevent malware attacks and the penetration of dangerous data. It is interesting to note that AlmaLinux and other RHEL-based Linux distributions use firewalls to manage firewall rules. Before we start and explain to you the methods of Secure Your AlmaLinux with Firewall, we recommend you choose and buy a plan from the Linux VPS server plans presented on our website. After installing AlmaLinux on our servers, you will enjoy their high quality.
How to Secure Your AlmaLinux with Firewall
In the rest of this article, we will comprehensively teach you how to Secure Your AlmaLinux with Firewall.
Harden Access with SSH
If we want to describe SSH with a simple example, we should say that it is like the door of your house. Therefore, securing the front door will keep your home safe. When you purchase a Linux server, your service provider will provide you with SSH root access. To increase security, you should start with SSH access. In the following, we will teach you 5 ways to harden SSH access.
To carry out the steps that we will tell in the rest of this article, it is enough to open the configuration file using your desired text editor:
nano /etc/ssh/sshd_config
It is also necessary to save and exit the configuration file after completing each step. Then, to apply the changes, you must restart the sshd file by running the following command:
systemctl restart sshd
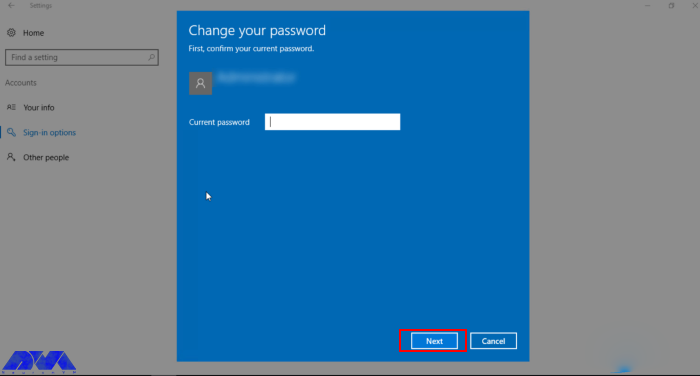
1: Setting an idle timeout
The first method is to exit SSH if the user is inactive. Therefore, you can search for the following command inside the configuration file:
#ClientAliveInterval 0
Now, if you want to set the idle time to 5 minutes, for example, you need to set it in seconds. That is 300 seconds:
ClientAliveInterval 300
2: Limit the maximum authentication attempts
In the second method, you can reduce the number of unsuccessful attempts to enter the system. (3 unsuccessful logins):
MaxAuthTries 3
3: Changing the SSH Port number
Another very effective method is to change the SSH port. Given that the default SSH port is 22, you can easily change it to the desired number by running the following command. (for example port 1022):
#Port 22
and change it to:
Port 1022
4: Disable Tunneling and forwarding
It should be noted that SSH tunnels allow connections made to a local port to be forwarded to a remote device over a secure channel. To disable some unnecessary options related to tunneling and forwarding, you can search for the following commands in the configuration file:
#AllowAgentForwarding yes
#AllowTcpForwarding no
#PermitTunnel no
Now you need to change the above commands as below and save the configuration file and exit it:
AllowAgentForwarding no
AllowTcpForwarding no
PermitTunnel no
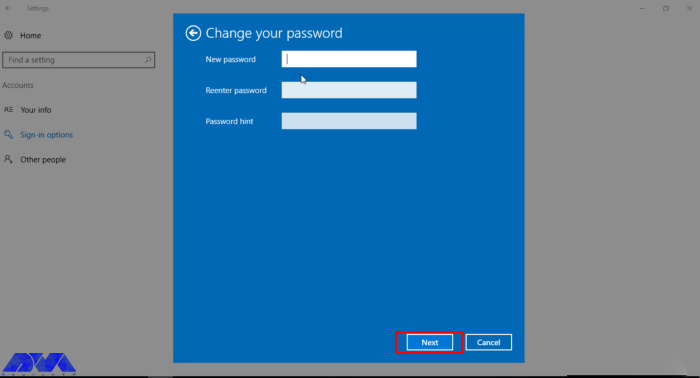
5: Using authentication without a password and public key
To generate your public key on a desktop computer on different platforms, you need to do the following. If you are using OpenSSH Client on Windows, you must use the following command in the command prompt:
ssh-keygen
But if you don’t use OpenSSH Client, you can generate SSH keys using PuTTYgen.
Also, if you use MacOS or Linux operating systems, you can use the following command:
ssh-keygen
Again, it is necessary to run the configuration file after entering the server by running the following command:
nano /.ssh/authorized_keys
Put your public key in a row in the file and save it. After doing this you can connect to SSH using your private key. Now it’s time to run the following command:
/etc/ssh/sshd_config
Finally, you need to paste the following lines in the desired path:
Password Authentication yes
PubkeyAuthentication yes
Installing CSF Firewall
AlmaLinux has a default firewall but we recommend CSF firewall for intrusion detection, intrusion detection, and security in this article. This firewall is very popular among the users of the popular control panels CPanel, DirectAdmin, and Webmin. To install the CSF firewall, you must first install the necessary prerequisites using the following command:
dnf install perl-libwww-perl.noarch perl-LWP-Protocol-https.noarch perl-GDGraph wget tar perl-Math-BigInt
Now you can run the following commands to download, extract and install CSF Firewall:
cd /usr/src
wget https://download.configserver.com/csf.tgz
tar -xzf csf.tgz
cd csf
sh install.sh
In the next step, you can use the following command to check if your server has iptable modules or not:
perl /usr/local/csf/bin/csftest.pl
After learning the relevant explanations, you should turn off the test mode:
sed 's/TESTING = "1"/TESTING = "0"/g' /etc/csf/csf.conf
Finally, you can restart the CSF firewall by running the following command:
csf -r
Install ClamAV Antivirus
ClamAV is an open-source, cross-platform, anti-malware toolkit developed by Cisco Systems Inc. This kit contains a new protection system to deal with Trojans, viruses, worms, and other types of malware. This antivirus is basically a light and command-line-based system that is combined with other tools such as FreshClam, ClamDaemon, ClamDTop, ClamScan, and Clamtk and offers many valuable features such as automatic database update and real-time scanning and scheduled scanning.
You can run the following commands to install ClamAV on AlmaLinux:
dnf install clamav
dnf install clamd
You should know that ClamAV uses FreshClam to check for new database versions periodically. Run ClamAV to update the signature database. To do this, just follow the instructions below step by step.
Stop the freshclam service by running the following command:
systemctl stop clamav-freshclam
You can also run Freshclam using the following command:
freshclam
Run the following command again to start the Freshclam:
systemctl start clamav-freshclam
After completing the installation process, you can use the following command to run a full system scan and remove malware:
clamscan --infected --recursive --remove /
AlmaLinux update
As you know AlmaLinux is a binary-compatible fork of the RHEL and CentOS base. On the other hand, RHEL and CentOS are secure enough for an enterprise environment. However, it is important to try to always keep AlmaLinux up-to-date by running the following command:
dnf update all
How to enable the Firewall on AlmaLinux
In the first step, you can check the status of the firewall on AlmaLinux by running the following command:
systemctl status firewalld
Check the services configured in the firewall using the following command:
sudo firewall-cmd --list-all
You can stop the firewall with the help of the following command:
sudo systemctl stop firewalld
You can also run the following command to start the firewall again:
sudo systemctl start firewalld
To restart the process, use the following command:
sudo systemctl restart firewalld
As you know, by default, the firewall starts automatically after the system boots. To disable the firewall, you can use the following command:
systemctl disable firewalld
It should be noted that if the above command is executed with the systemctl stop firewalld command, the firewall will be disabled forever.
The interesting thing is that you can reactivate the firewalld service at any time:
sudo systemctl enable firewalld
Conclusion
In this article that you read, we tried to fully familiarize you with the steps to secure AlmaLinux so that you can be safe from cyber-attacks. We also tried to teach you how to Secure Your AlmaLinux with Firewall. In this way, now you can easily install FirewallD on AlmaLinux and other RPM-based Linux systems. By doing this you will partially secure your system from the outside world.