In today’s evolving digital landscape, Safeguarding digital assets from potential attacks is more important than ever. With cyber threats increasing alarmingly, businesses and individuals need a reliable and effective solution to protect their sensitive information. Enter Nessus, the key to fortifying your digital fortress against potential vulnerabilities. As a powerful vulnerability scanning tool, Nessus provides comprehensive insights into your network’s security posture, allowing you to identify and fix potential vulnerabilities before malicious actors exploit them. With its advanced features and user-friendly interface, Nessus empowers organizations of all sizes to proactively defend their digital assets, ensuring peace of mind and maintaining the trust of customers and stakeholders. In this article, we’ll look at the incredible capabilities of Nessus and explore how this essential tool can revolutionize your cybersecurity strategy. Get ready to unlock a more secure digital future with Nessus.
Understanding the Importance of Safeguarding Digital Assets
Protecting digital assets is of great importance in today’s world, which is completely dependent on virtual and digital technologies. In this regard, the users of these technologies have obtained assets that are offered digitally. These assets are information, data, and valuable resources such as personal information, material data intellectual property, and sometimes business strategies. Here we will mention some cases of safeguarding digital assets:
– Financial security especially for businesses.
– National security at the level of government and public institutions
– Customer loyalty in businesses and organizations.
– Safeguarding digital assets to manage the reputation of organizations.
– Respect data privacy and protection for sensitive personal and financial information.
We suggest you use the high-speed Windows VPS servers provided on our website for investing and trading in digital markets.
Common Types of Cyber Attacks
Cyber attack is the attempt of cyber criminals and hackers to gain access to computer systems. The purpose of this attack is to change, steal, disclose information, or destroy systems. This action is very dangerous and may target a wide range of users of organizations and companies. The purpose of hackers is to gain access to sensitive and valuable company resources for profit and abuse. Let’s examine some of these attacks in the digital world:
1- Phishing: This is a kind of cyberattack that uses email, SMS, social media, phone, and social engineering techniques to encourage victims to share sensitive information like passwords.
2- Malware: This is a kind of malicious software like a code or program that is created to harm a computer or system. This one is the most common type of attack.
3- Dos and DDoS attacks: This malicious and targeted attack, floods a network with false requests to ruin business operations. The significant difference between Dos and DDos is that Dos originates from just one system while DDos starts from multiple systems.
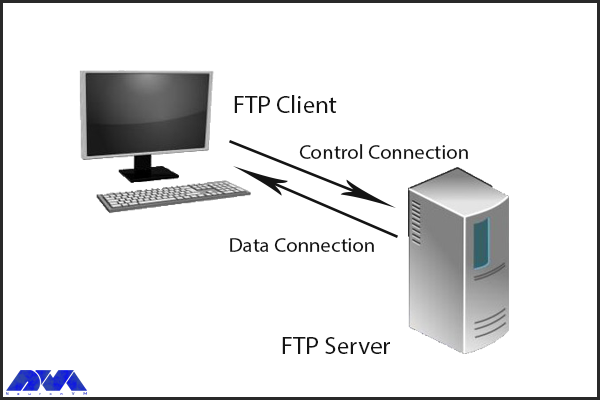
4- Spoofing: This attack is a technique that is used by a cybercriminal to disguise himself as a trusted and known source.
5- Code injection attacks: An injection attack includes injecting malicious code in a vulnerable computer or network to change the course of action.
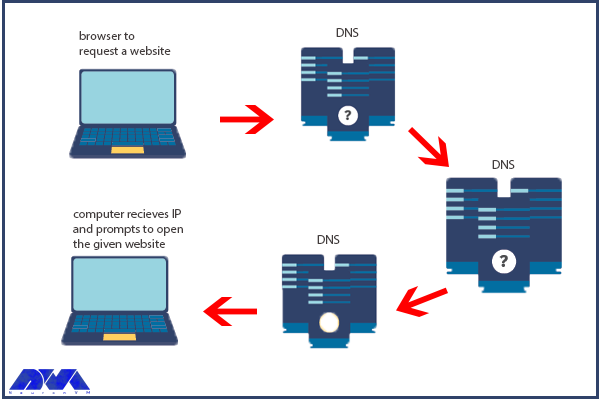
6- DNS Tunneling: This type of cyber attack works in such a way that it uses DNS questions and answers to bypass security operations and transfer code data in the network.
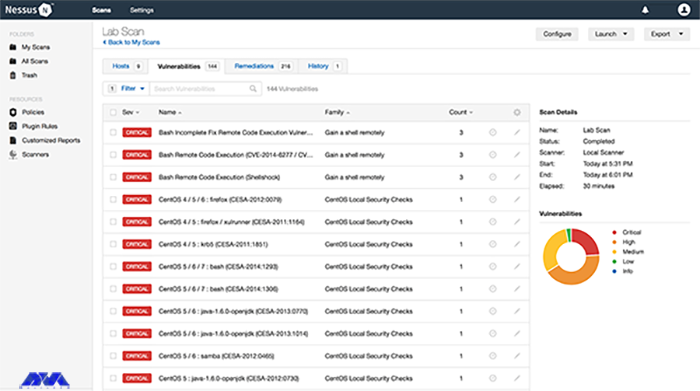
How Nessus Works as a Vulnerability Scanner
Nessus is a scanning tool that performs its scans through several plugins that run on every host on the network to detect vulnerabilities. These plugins are considered separate pieces of code that Nessus uses to perform individual scans. These plugins have extensive features. For example, a plugin can be launched and placed on a specific host to do the following:
- Operating system identification and services run on ports.
- Identifying vulnerable software components.
- Determining whether compliance requirements are met on different hosts.
Safeguarding Digital Assets
Benefits of Using Nessus for Vulnerability Assessment
– A valuable benefit of Nessus is the creation of a fast and user-friendly method to find and fix vulnerabilities in many IT assets, containing cloud-based and virtualized resources.
– Over 450 pre-configured templates are provided for standard vulnerability scans and configuration audits to simplify platform usage.
– Another benefit of Nessus is its low false positive rate of 0.32 defects in every 1 million scans. If there is too many false positive, it can suppress security teams cause alert fatigue, and ignore legitimate threats.
– It is beneficial for security professionals because it is a highly portable, and helpful tool.
Key Features of Nessus
Nessus has great features like:
1) Ability to discover assets at high speed
2) The capability of listening to the configuration
3) Ability to detect and detect malware
4) The feature of discovering sensitive data
Steps to Implement Nessus for Digital Asset Protection
Nessus is a vulnerability scanner and assessment tool that can help protect digital assets by identifying and prioritizing security vulnerabilities. The implementation of Nessus for the protection of digital assets has several steps, which are as follows:
1- It is time to download and install Nessus, so go to the Nessus Home landing page, enter your name and email address, and then click on the register button. Since you want to install it on your system, Click download.
2- As you downloaded Nessus, run the installation package and follow the given instructions to complete the installation.
Tip: Nessus will create a local server on your computer and run from there.
3- Now go to your browser and insert https://localhost:8834/ to complete the sign-up and activate your Nessus copy. You will encounter the message “Your connection is not secure“. Go to “advanced” and then “proceed to localhost” to bypass the warning.
4- Create an account and leave the registration as “Home, Professional, or Manager,” then enter the activation code and press continue. At last, Nessus will download several plugins to scan your network.
5- Now you have a Nessus scanner and you can test it on your network. go through the instructions below:
– Click on New Scan.
– Then click on Network Basic Scan.
– Choose a name for your scan and add a description.
– In the “Targets” field, enter IP scanning details about your network, and Nessus will scan all the devices on your network.
– Click the Save button and on the next part, click on the Play icon to start the scan.
Best Practices for Using Nessus Effectively
You can use Nessus to identify security weaknesses in networks, systems, and applications. These are the best practices for Nessus:
– Try to keep Nessus up-to-date.
– Configure scan policies.
– You should scan segmented networks.
– It is recommended to schedule the scan appropriately.
– You should review and validate the results.
– It is better to prioritize vulnerabilities, you can use the CVSS score or Common Vulnerability Scoring System.
Case Studies of Successful Vulnerability Assessments Using Nessus
To demonstrate the effectiveness of Nessus as a vulnerability scanning tool, let’s explore some real-world case studies:
1. **XYZ Corporation**: XYZ Corporation, a global financial institution, implemented Nessus as part of its vulnerability management strategy. By conducting regular scans and prioritizing remediation efforts, the company significantly reduced its vulnerability. This proactive approach resulted in a 50% reduction in successful cyber attacks and increased customer trust.
2. **ABC Healthcare**: ABC Healthcare, a leading healthcare provider, used Nessus to assess the security posture of its network infrastructure and medical devices. By identifying vulnerabilities and implementing appropriate controls, the organization improved patient data protection and achieved compliance with regulatory frameworks such as HIPAA.
3. **DEF Manufacturing**: DEF Manufacturing, a large-scale manufacturing company, integrated Nessus with its SIEM system to enhance threat detection capabilities. By leveraging the real-time data provided by Nessus, the organization was able to quickly identify and respond to potential vulnerabilities, minimizing the impact of cyber-attacks and ensuring uninterrupted operations.
Comparing Nessus with Other Vulnerability Scanners
In this section, we will try to compare Nessus with some other vulnerability scanners like Openvas, Openscap, and Rapid7nexpose.
Openvas: OpenVAS is open-source and is often compared to Nessus due to its similar feature set. Both tools have a plugin-based architecture to identify vulnerabilities in systems. Since OpenVAS is free to use, it is suitable for budget-conscious organizations. However, Nessus is better known for its performance, user interface, and support.
Rapid7nexpose: Nexpose or InsightVM is another popular vulnerability management tool that can be compared to Nessus. This tool provides real-time vulnerability assessment and risk analysis. Rapid7expose offers additional features such as usability evaluation and integration with other Rapid7 products. Nessus, on the other hand, has a wider user base and may have a wider library of vulnerability checks.
Openscape: Openscape is also an open-source, compliance-friendly scanner that focuses entirely on security standards. Assessing compliance with security standards and policies is the main task of this scanner, so it is an excellent choice for organizations with compliance requirements. But Nesus provides a more comprehensive vulnerability scan.
Conclusion: Importance of Proactive Vulnerability Management with Nessus
With cyber threats becoming increasingly sophisticated, organizations and individuals need a reliable and effective solution to protect their sensitive information. As a powerful vulnerability scanning tool, Nessus provides the key to fortifying your digital fortress against potential vulnerabilities.
By implementing Nessus as part of your vulnerability management strategy, you can proactively identify and address potential weaknesses in your network infrastructure and applications. The comprehensive insights provided by Nessus enable you to prioritize remediation efforts and reduce the risk of exploitation. With its cutting-edge features, scalability, and ease of use, Nessus empowers organizations of all sizes to defend their digital assets effectively.
In an era where the consequences of a successful cyber attack can be devastating, Nessus offers peace of mind and ensures the continuity of your operations. By investing in proactive vulnerability management with Nessus, you can unlock the door to a safer digital future and maintain the trust of both customers and stakeholders. Safeguard your digital assets today with Nessus and fortify your defenses against potential attacks.
FAQ
It is a fast and user-friendly tool to find and fix vulnerabilities in most IT assets like cloud-based and virtualized resources.
Nessus is free to use and scan any environment but it is limited to 16 IP addresses per scanner.