In recent years, virtual private servers (VPS) have become increasingly popular among traders in the financial markets. A VPS offers many advantages for traders, including high-speed and reliable internet connectivity, uninterrupted trading operations, and the ability to run automated trading strategies 24/7. However, to make the most of trading on VPS, it is essential to follow certain best practices. Let’s discuss the best practices for trading on VPS.
Trading on VPS
Trading is a dynamic and ever-evolving practice that involves buying and selling financial instruments to capitalize on market movements. It is a fundamental activity in the financial markets, attracting individuals, institutions, and algorithmic trading systems alike.
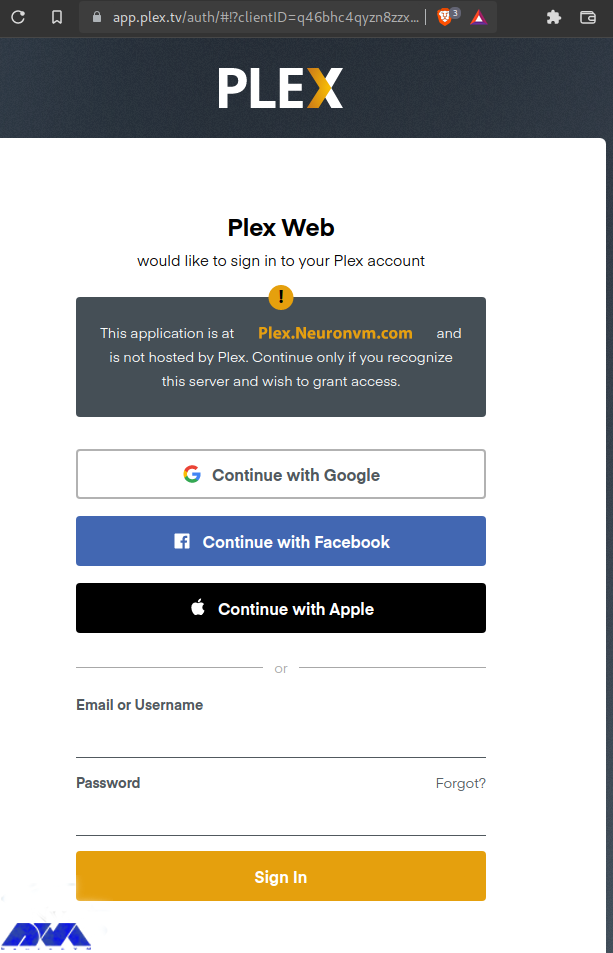
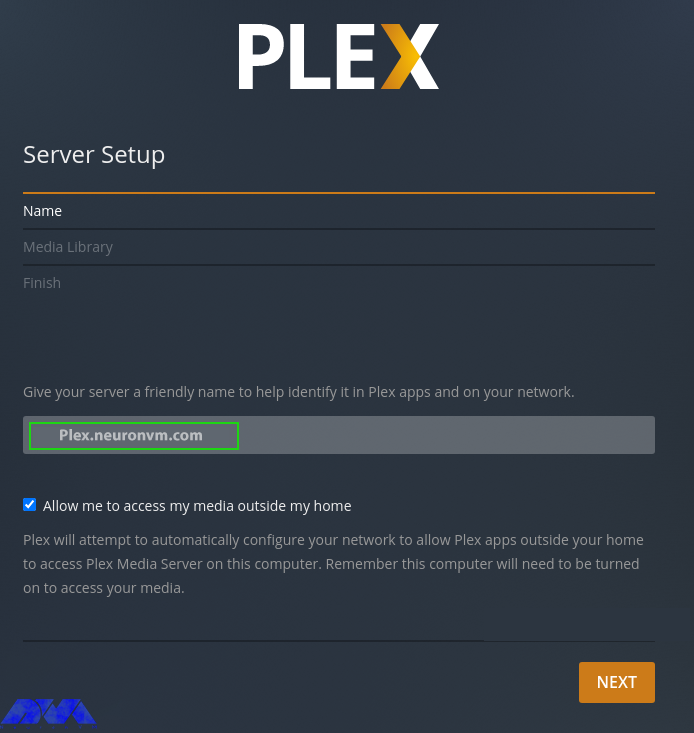
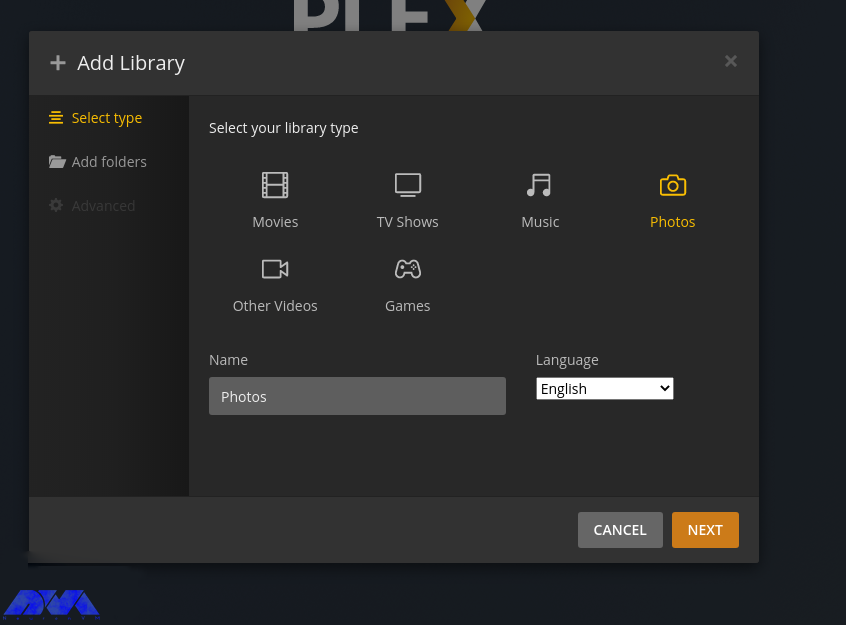
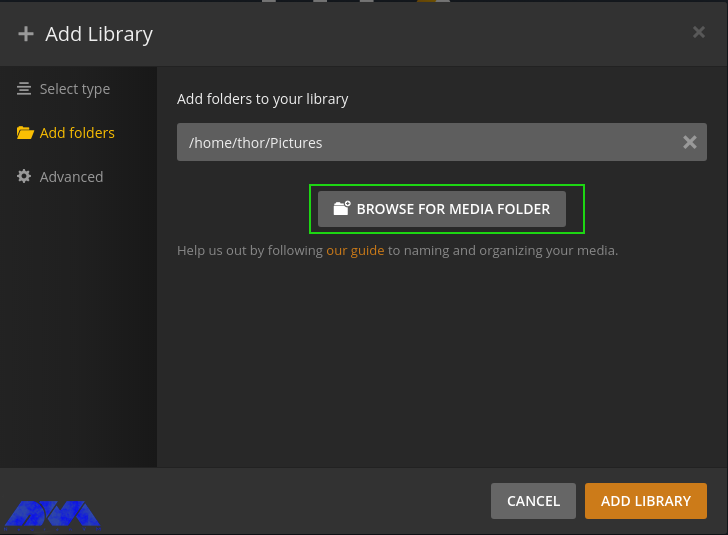
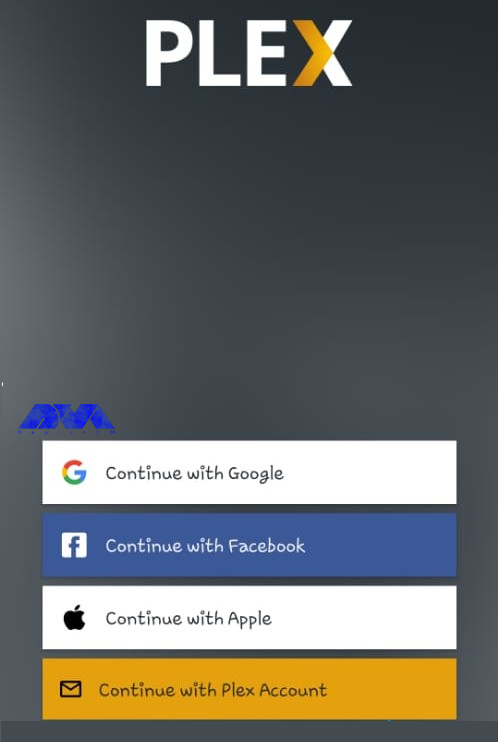
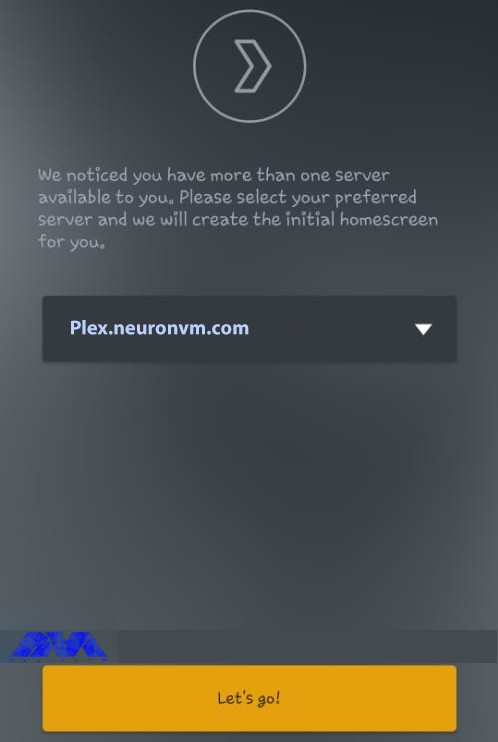
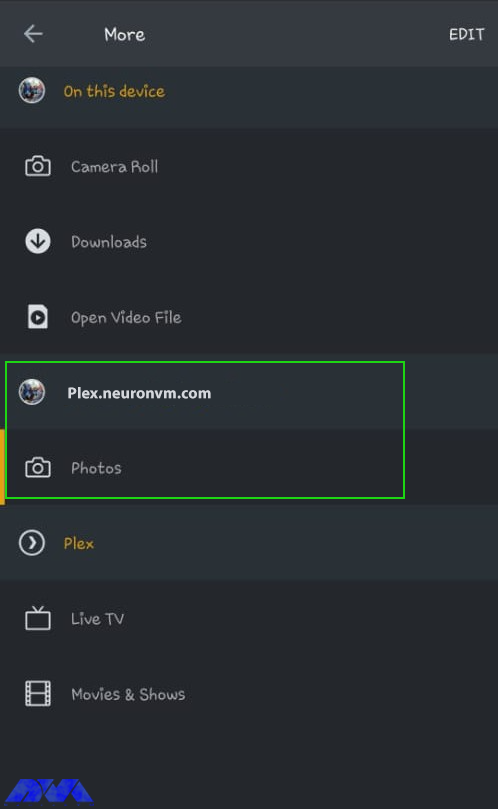
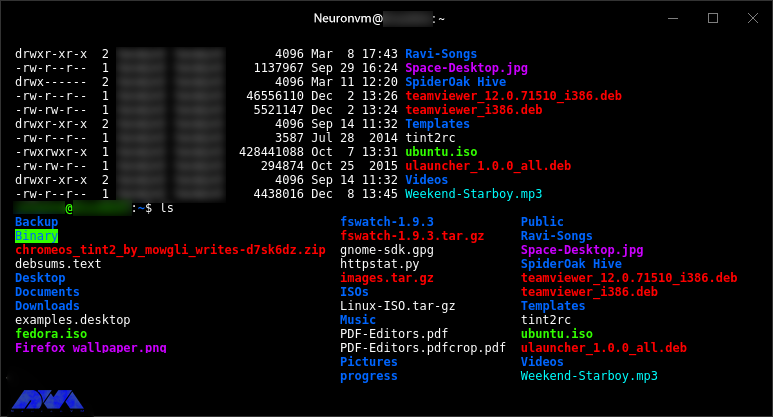
Trading on VPS refers to conducting trading activities using a VPS. A VPS is a virtual machine that runs its own copy of an operating system, allowing users to have full control over the server’s resources. We advise you to use Windows VPS servers offered on our website for trading and tell us your opinion about the high quality of our servers.

Exploring the Powerful Features of Trading on a VPS
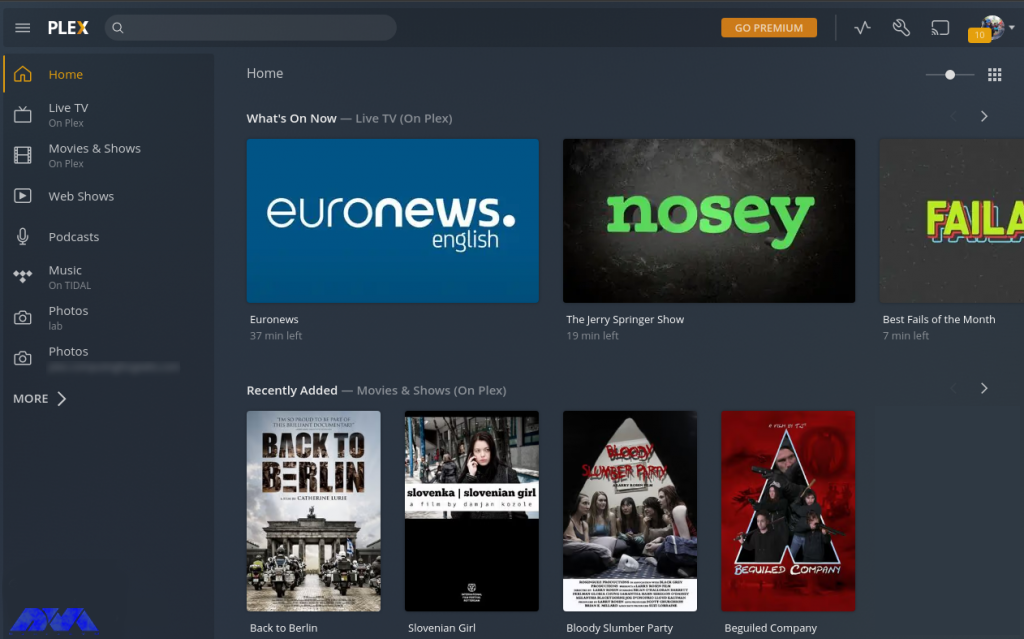
Trading on a VPS can provide traders with several powerful features that can enhance their trading experience. Here are some of the key benefits and features of trading on a VPS:
Enhanced Reliability and Uptime
One of the most significant advantages of trading on VPS is the enhanced reliability it provides. VPS servers are hosted in state-of-the-art data centers with redundant power supply and internet connectivity, ensuring maximum uptime. NeuronVM VPS servers are built on cutting-edge technology, ensuring maximum uptime and seamless trading operations.
With redundant power supply, high-speed internet connectivity, and state-of-the-art infrastructure, you can trade with confidence, knowing that your trading platform will remain online 24/7.
Enhanced Execution Speed
In the world of trading, speed is crucial. VPS hosting enables traders to achieve ultra-low latency and lightning-fast execution speeds. By leveraging high-speed internet connections and powerful server infrastructure, NeuronVM VPS allows for quick order placement and execution.
This is particularly advantageous for high-frequency traders and those who rely on split-second decisions. With faster execution speeds, traders can capitalize on market opportunities and potentially increase their profitability.
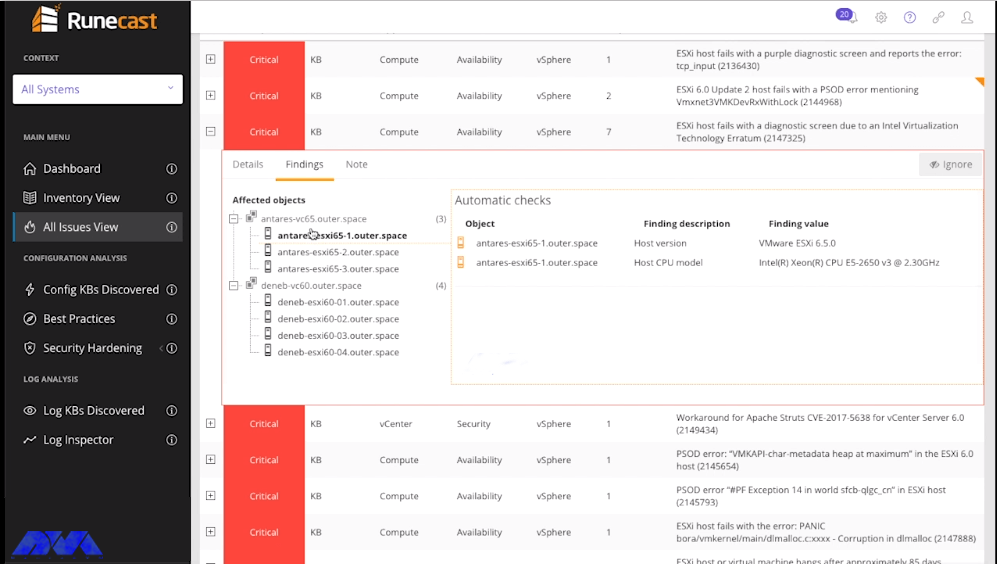
Robust Security Measures
Security is a paramount concern for traders, given the sensitive nature of financial transactions. NeuronVM VPS servers prioritize the security of your trading operations, employing advanced security measures to safeguard your data and transactions.
With NeuronVM’s secure infrastructure, you can trade with peace of mind, knowing that your confidential information is protected from unauthorized access.
Flexibility and Scalability
NeuronVM VPS servers offer traders unmatched flexibility and scalability. Whether you are an individual trader or a financial institution, NeuronVM provides customizable VPS hosting plans to meet your specific requirements.
You can easily scale up or down your resources based on your trading needs, ensuring optimal performance and cost-effectiveness.
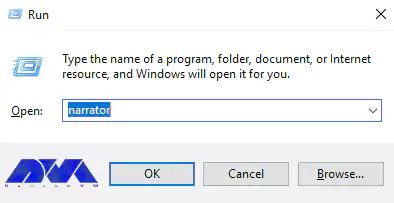
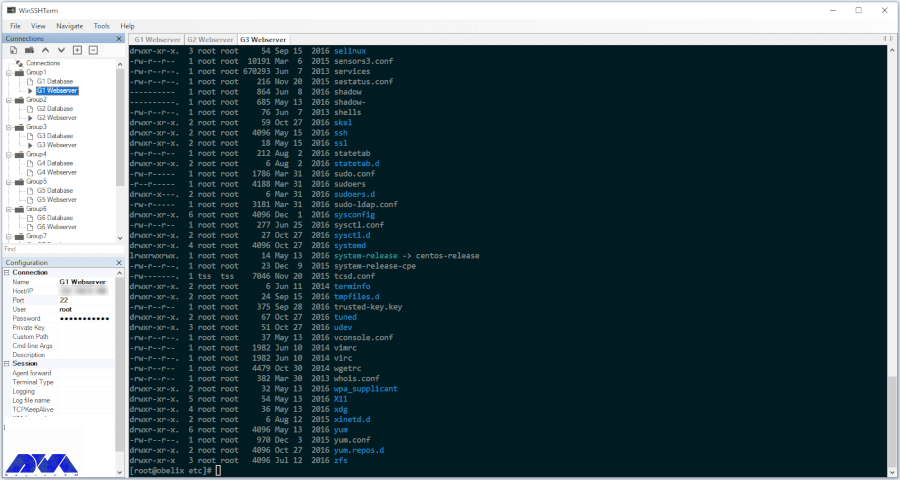
Remote Accessibility
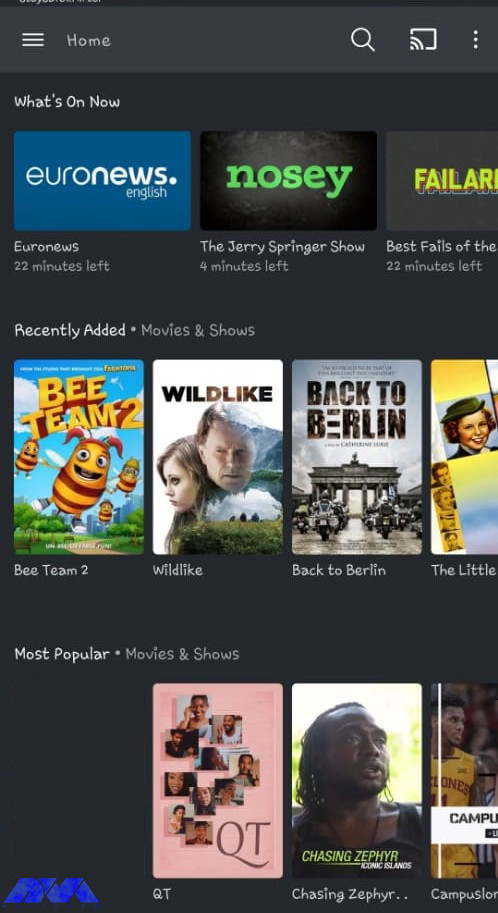
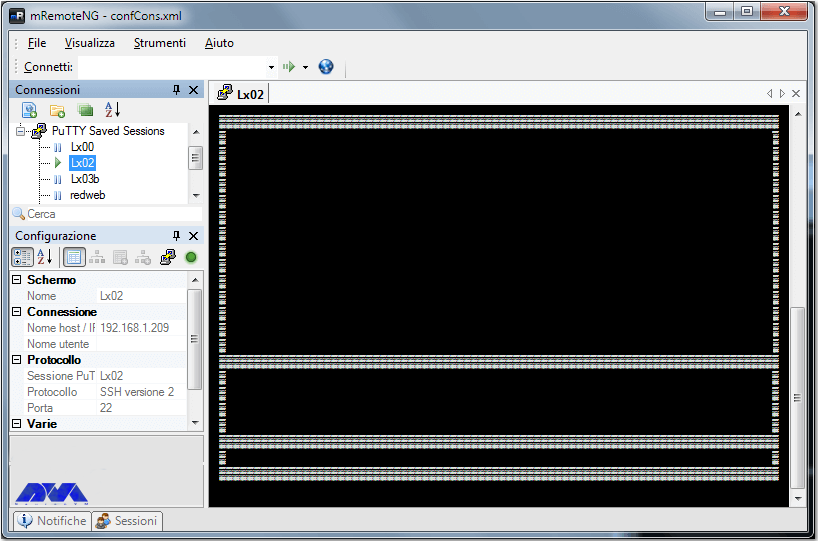
Trading on VPS eliminates the constraints of being tied to a specific location. With NeuronVM’s VPS servers, you can access your trading platform from anywhere in the world, as long as you have an internet connection.
Whether at home, in the office, or on the go, you can monitor your trades, execute orders, and adjust strategies in real-time.
Choose a Reliable VPS Provider
The first and most crucial step in trading on a VPS is to select a reliable VPS provider. Look for a provider that offers low latency connections, high uptime, and excellent customer support. Ensure that the VPS provider has data centers located in regions close to the financial markets you trade in, as this reduces latency and improves trade execution speed.

NeuronVM offers VPS hosting specifically designed for trading purposes. They provide low-latency servers located in major financial hubs around the world, ensuring fast and reliable connection speeds. Also, our website offers high uptime guarantees and robust security measures to protect your trading activities.
Optimize Network Connectivity
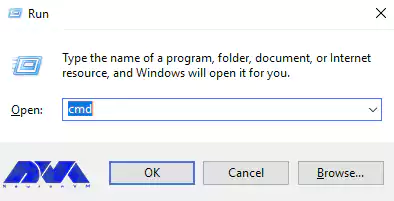
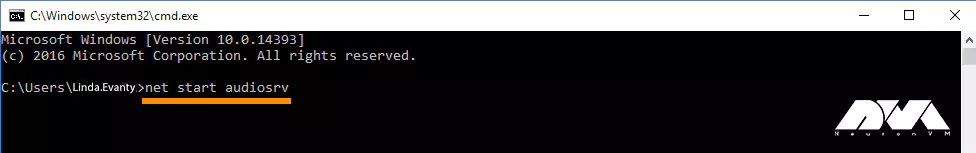
Network connectivity plays a crucial role in trading. To ensure a smooth trading experience, we recommend you optimize your VPS’s network connectivity. Here are a few different ways to do this:
- Choose a Reliable Internet Service Provider (ISP): To ensure smooth trading operations, start by selecting a reliable Internet Service Provider (ISP) that offers low latency and high-speed internet connections. A stable and fast internet connection is essential for real-time data transmission and rapid execution of trades.
- Optimize Router Placement: The placement of your router plays a significant role in network performance. To maximize connectivity, position your router in a central location, away from obstructions such as walls or furniture. This allows for better signal distribution throughout your trading area.
- Use a Wired Connection for VPS: Wired connections offer lower latency and higher speeds, reducing the chances of data packet loss during transmission. By directly connecting your computer to the router via an Ethernet cable, you can ensure a stable and reliable network connection for trading on your VPS.
- Regularly Monitor and Optimize Network Settings: Ensure that your VPS is configured to prioritize trading applications, allocating sufficient bandwidth to them. You can also consider implementing Quality of Service (QoS) settings on your router to prioritize trading data over other internet activities, preventing potential delays or interruptions.
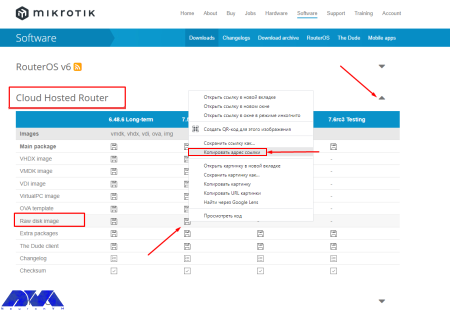
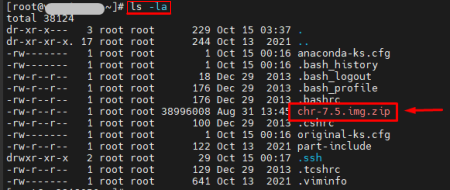
Install Reliable Trading Software
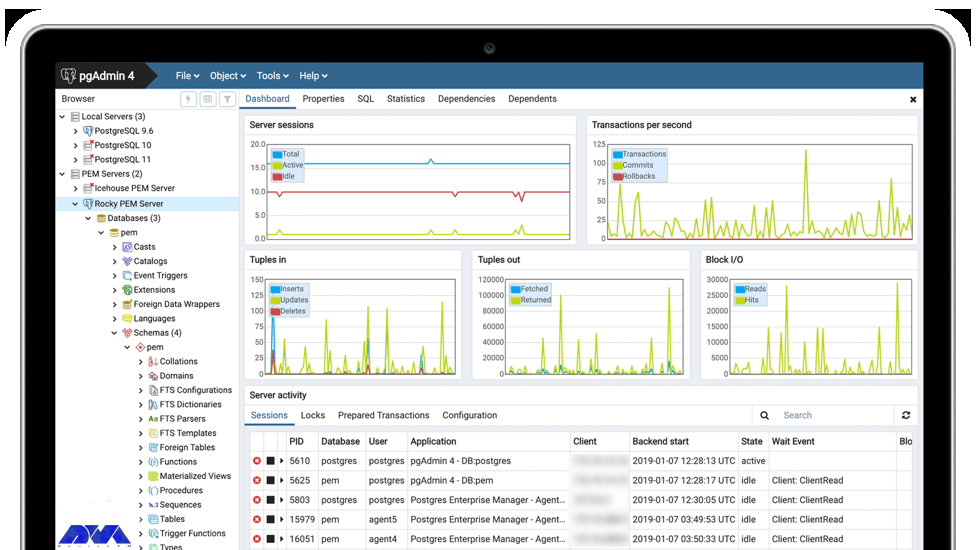
When trading on a VPS, it is essential to install reliable and trusted trading software. Choose a platform compatible with your trading strategy that provides features like real-time market data, advanced charting tools, and order execution capabilities.
1) Research and Choose Trusted Trading Software: Look for software that is specifically designed for trading and has a proven track record of reliability and performance.
Read reviews, seek recommendations from fellow traders, and consider the software’s features, user interface, and compatibility with your trading strategy. Some of the best trading software out there are MetaTrader 4 & 5, cTrader, NinjaTrader, TradeStation, and Interactive Brokers Trader Workstation.
2) Ensure Compatibility and Optimal Configuration: Check the software’s system requirements and ensure that your VPS meets or exceeds them. Additionally, consider the optimal configuration settings recommended by the software provider.
Adjusting settings such as memory allocation, CPU usage, and network protocols can enhance the performance and stability of the trading software on your VPS.
3) Regularly Update and Maintain Your Trading Software: Keep track of software updates provided by the vendor and install them promptly. Updates often include bug fixes, feature enhancements, and security patches that can improve the trading experience and protect your VPS from potential vulnerabilities.
It’s important to note that the best trading software for you will depend on your specific trading goals, strategies, and preferences. It’s recommended to explore and evaluate different platforms, considering factors such as ease of use, available features, reliability, and customer support before deciding.
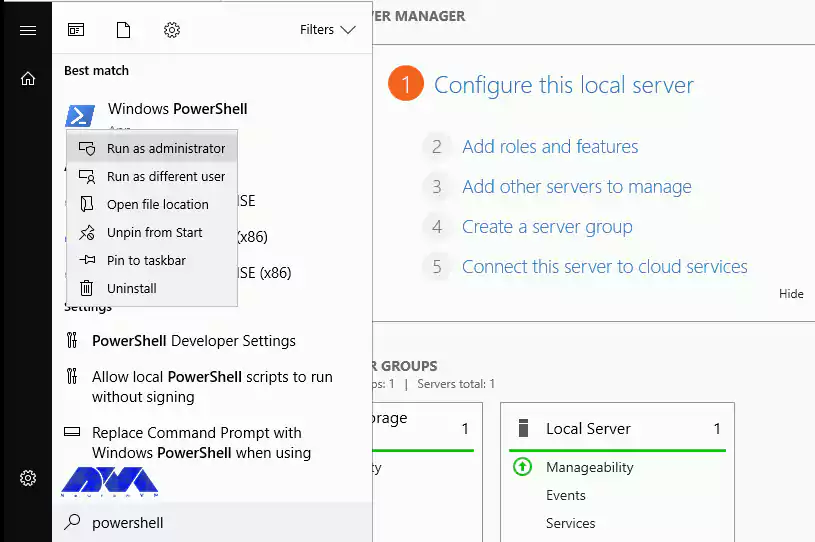
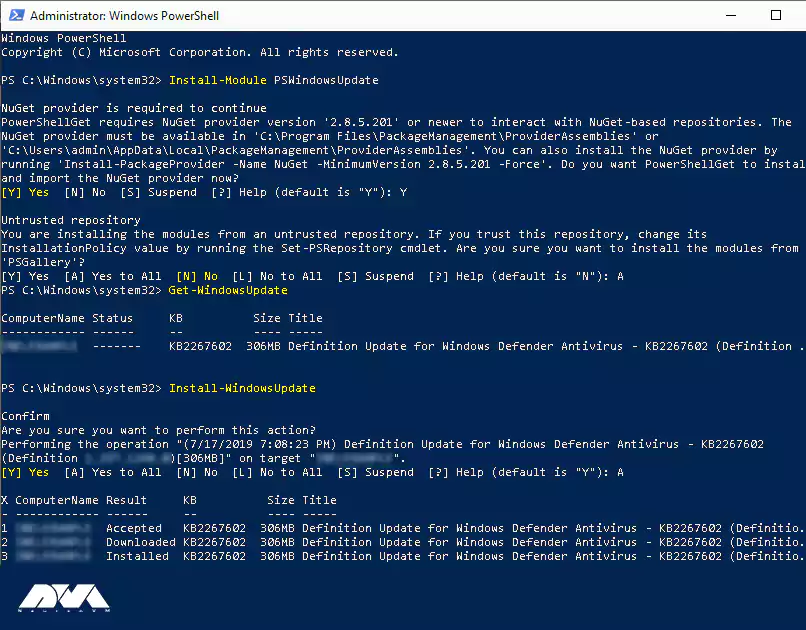
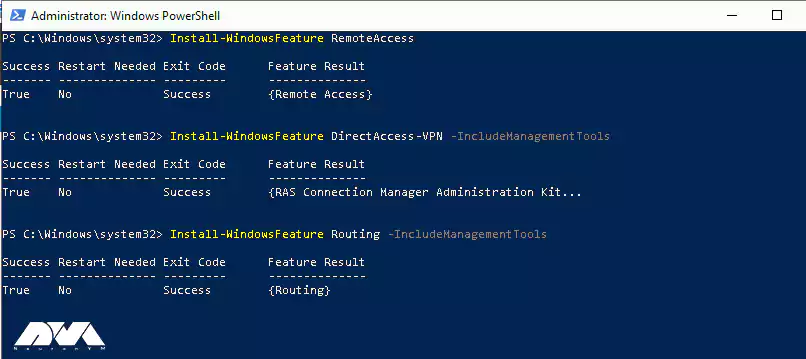
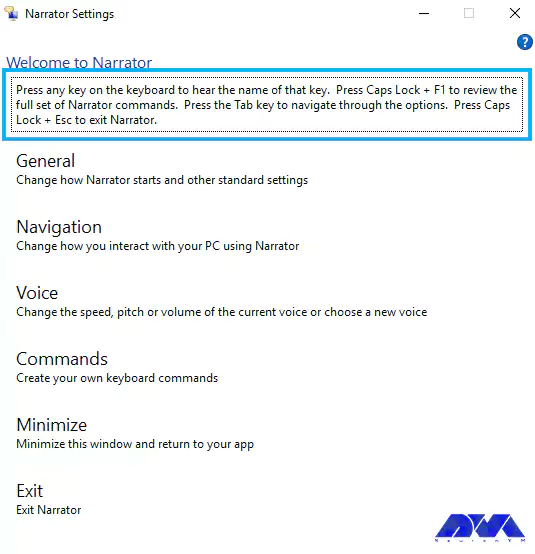
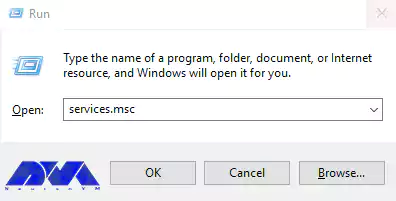
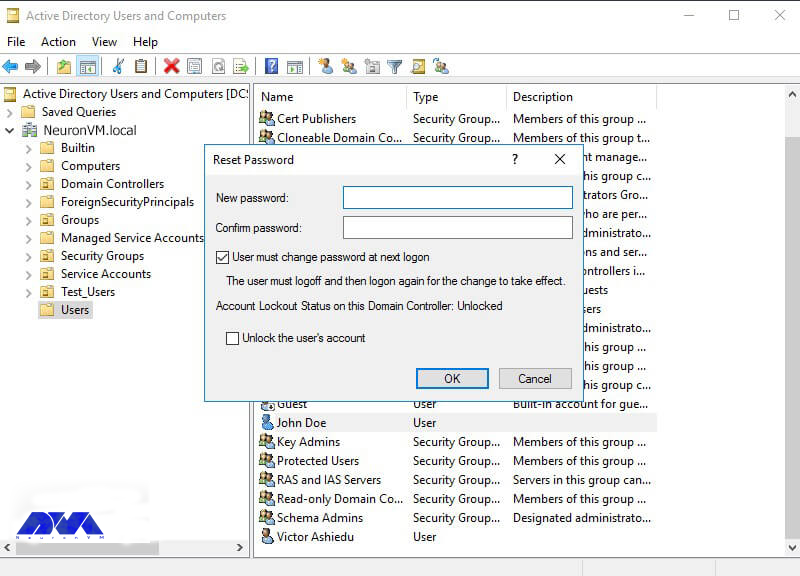
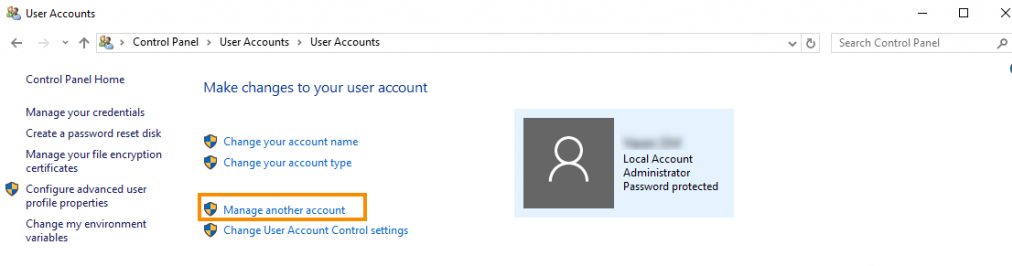
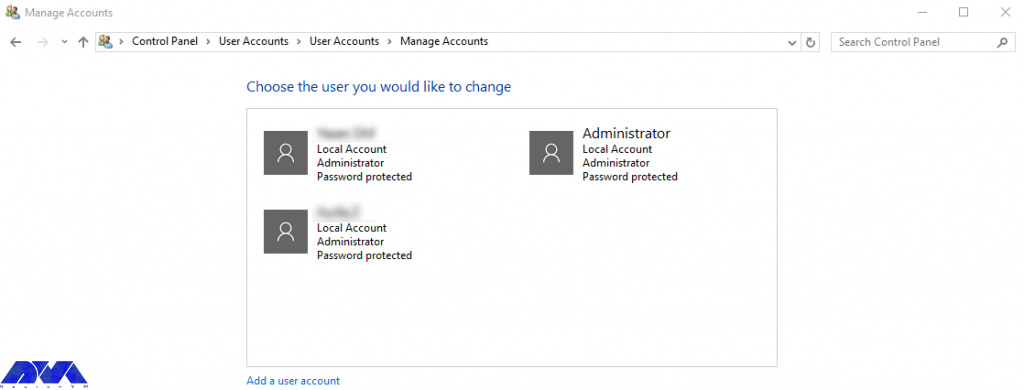
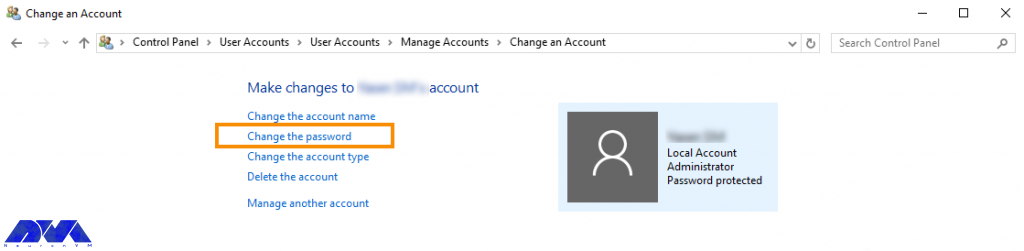
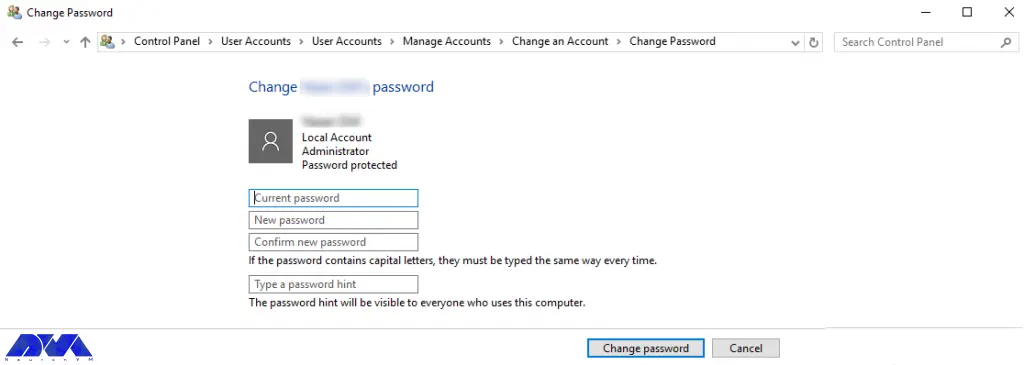
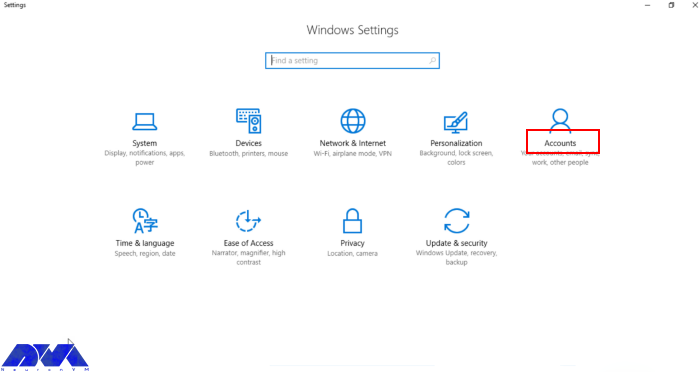
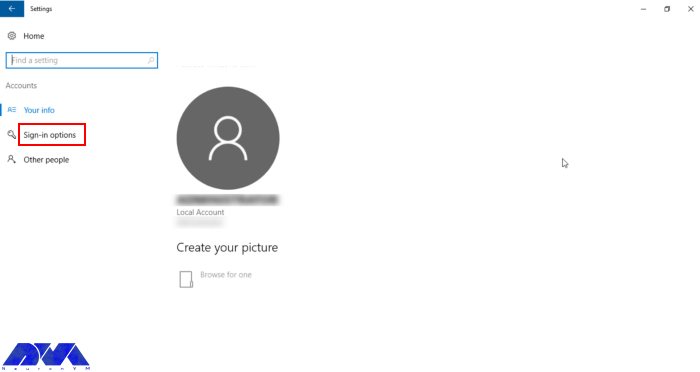
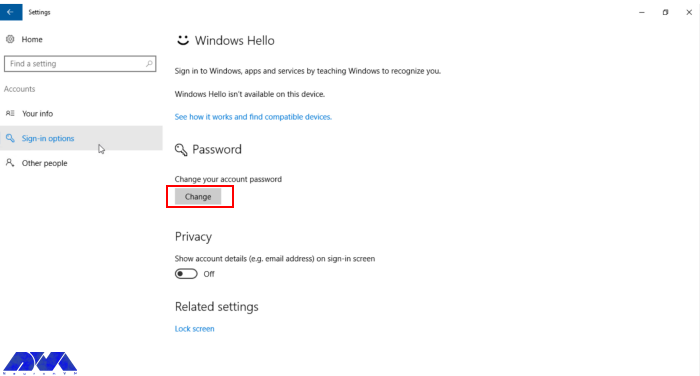
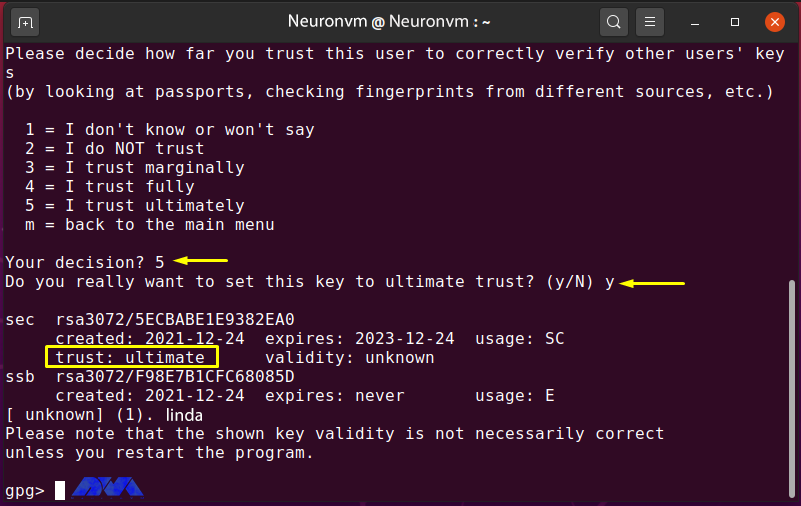
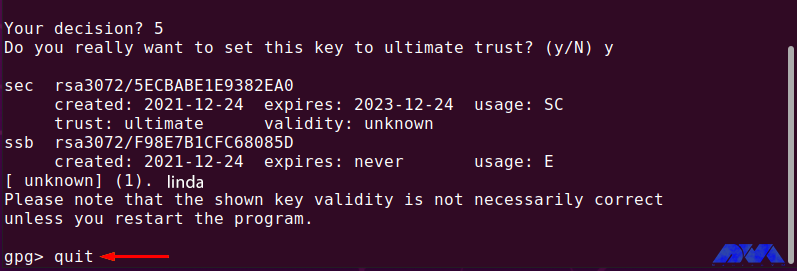
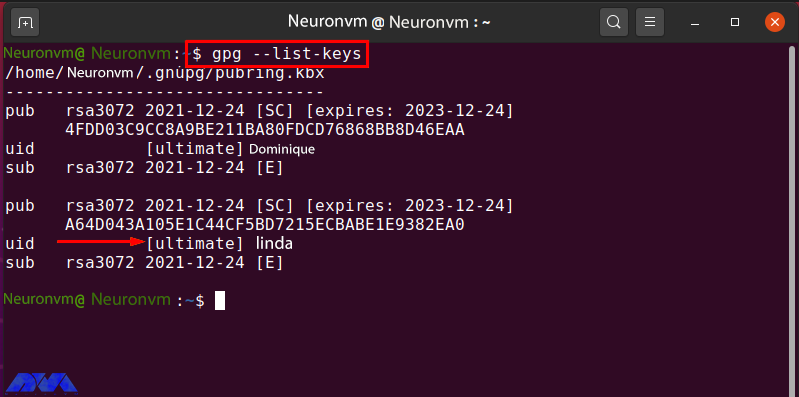
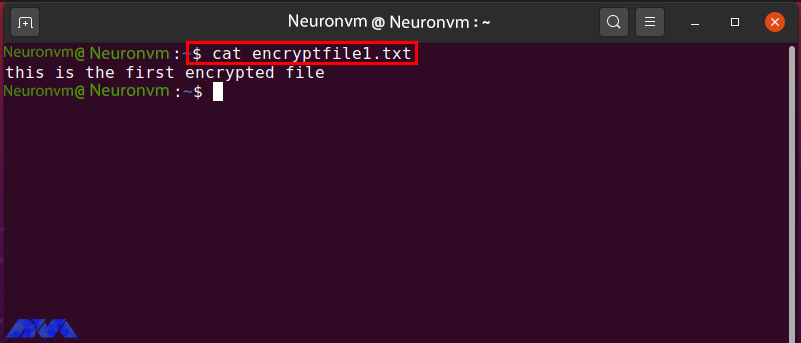
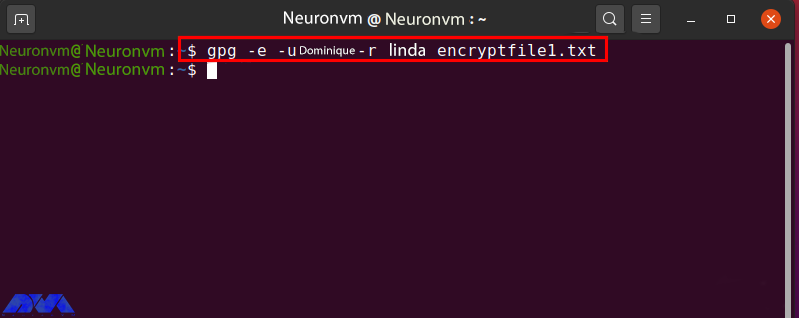
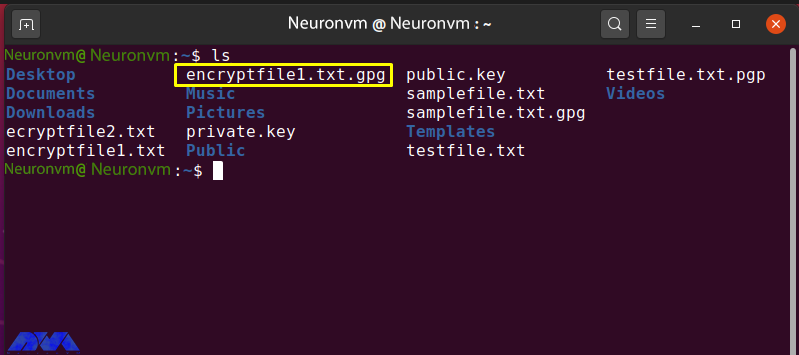
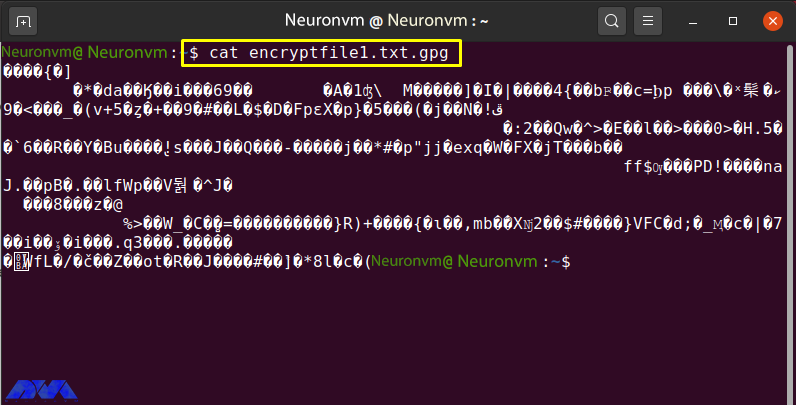
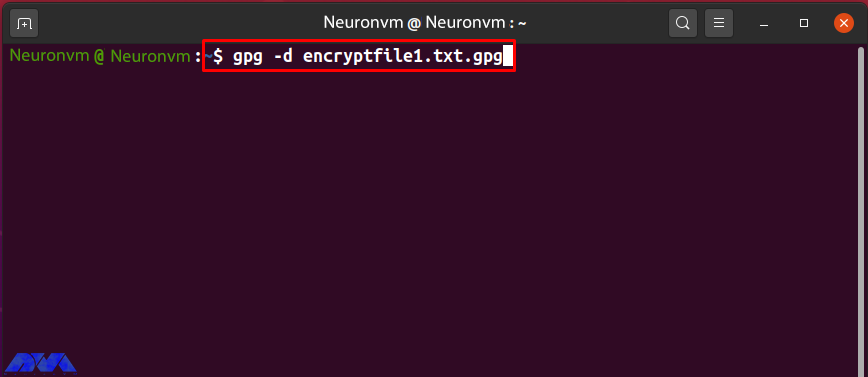
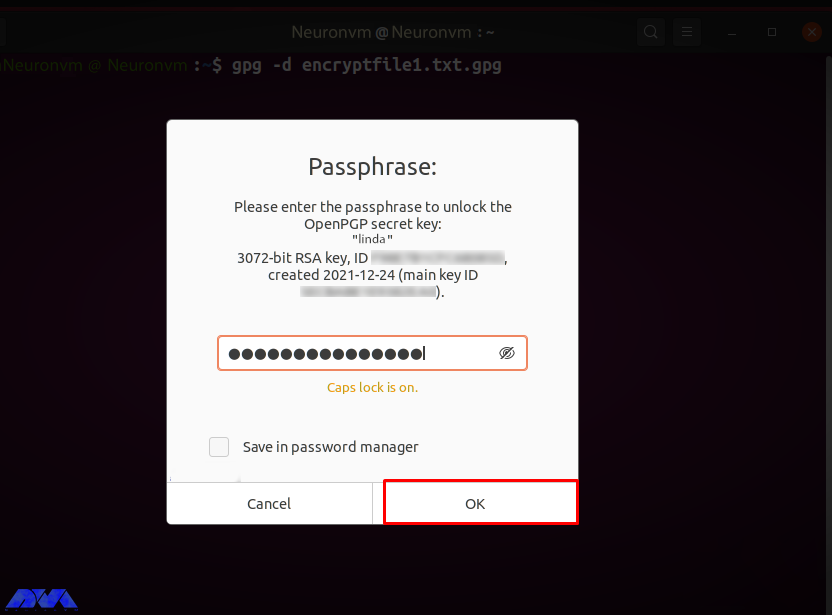
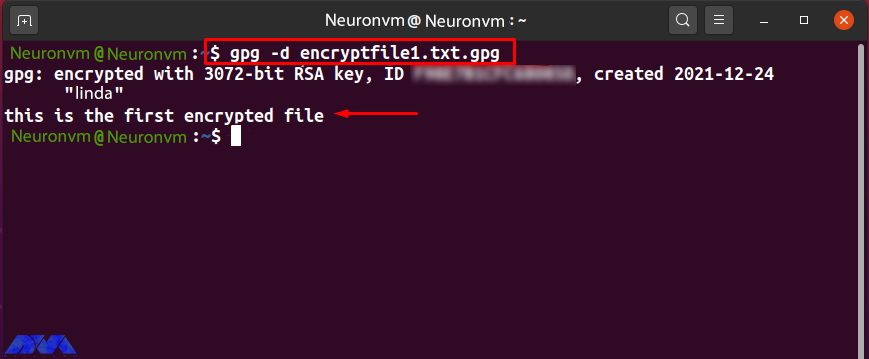
Maintain Proper Security Measures
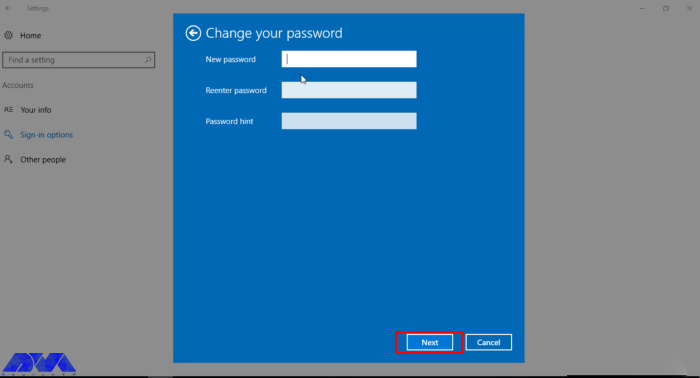
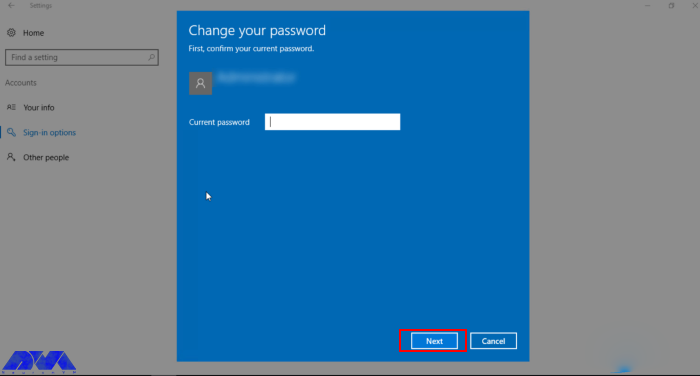
Security is paramount when trading on a VPS. Implement robust security measures to protect your trading activities and sensitive information. Use strong and unique passwords for your VPS login and trading platform accounts. Regularly update your antivirus software, firewall, and operating system to prevent any potential security breaches.

Backup Trading Data
It is crucial to regularly backup your trading data to avoid any loss in the event of hardware or software failures. Setup automated backups of your trading platform settings, indicators, templates, and trade history. Consider storing the backups on external storage devices or cloud-based solutions for added security.
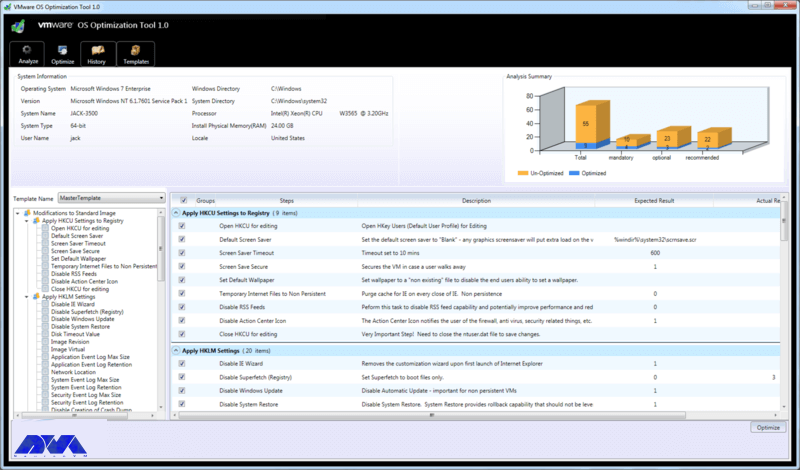
Monitor System Performance
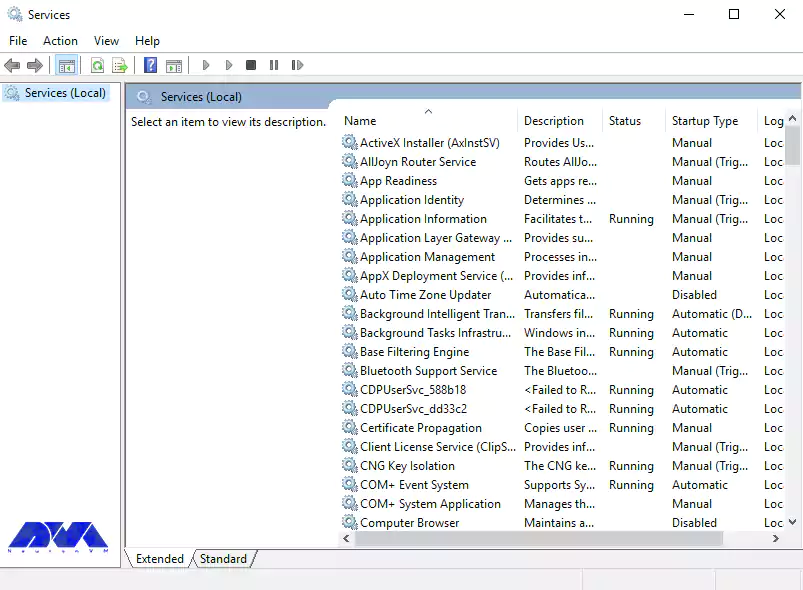
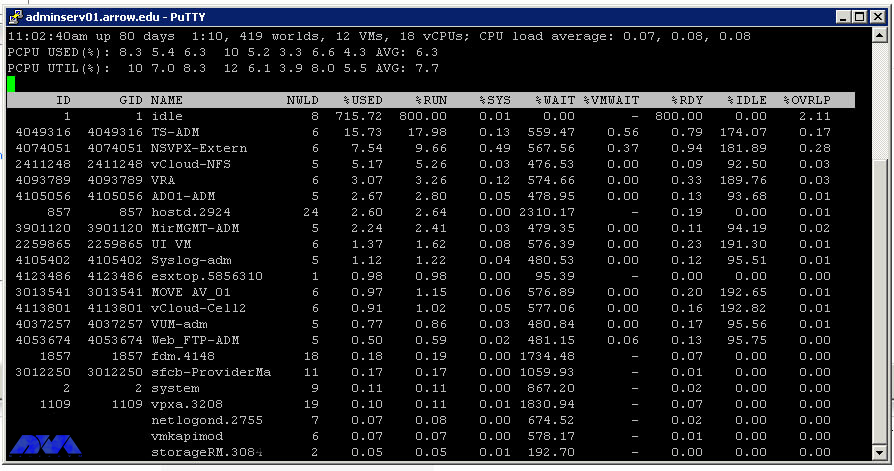
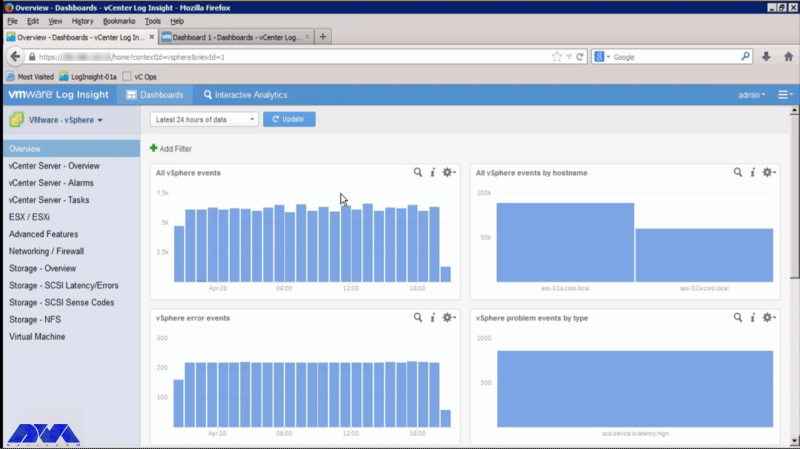
Keep a close eye on your VPS’s performance to ensure optimal trading conditions. Monitor the CPU and memory usage, network latency, and disk space utilization. If you notice any performance issues, investigate the cause and take the necessary steps to resolve them.
Regularly restart your VPS to clear any accumulated resources and maintain optimal performance.

Final Thoughts
Trading on a VPS can greatly enhance your trading experience by providing high-speed and reliable connectivity, uninterrupted trading operations, and the ability to run automated strategies. By following the best practices mentioned in this guide, you can maximize the benefits of trading on a VPS and improve your overall trading performance.