RedHat is a software company that combines open-source Linux operating system components with related applications into distribution packages that customers order. In this comprehensive article, we will tell you what is RedHat and introduce you to it completely.
Introduction To RedHat and its products
RedHat offers open-source software used by DevOps engineers and businesses, including operating system platforms, storage, middleware, and management products, as well as training, support, and consulting services. Dell, IBM, and Oracle also support the RedHat platform and open-source application community.
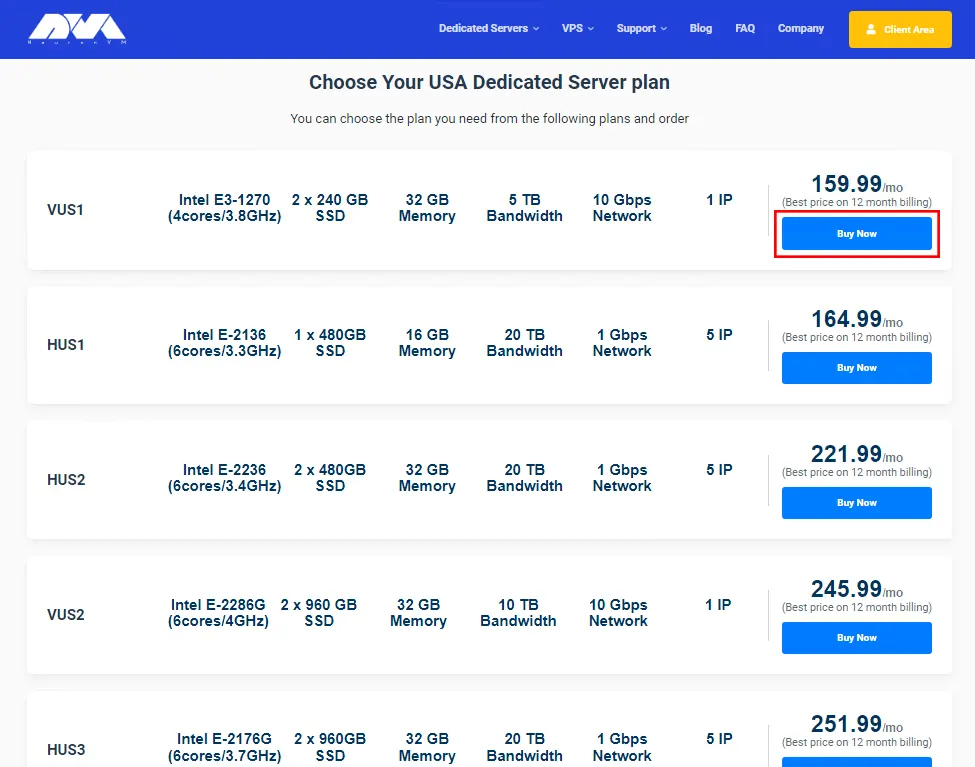
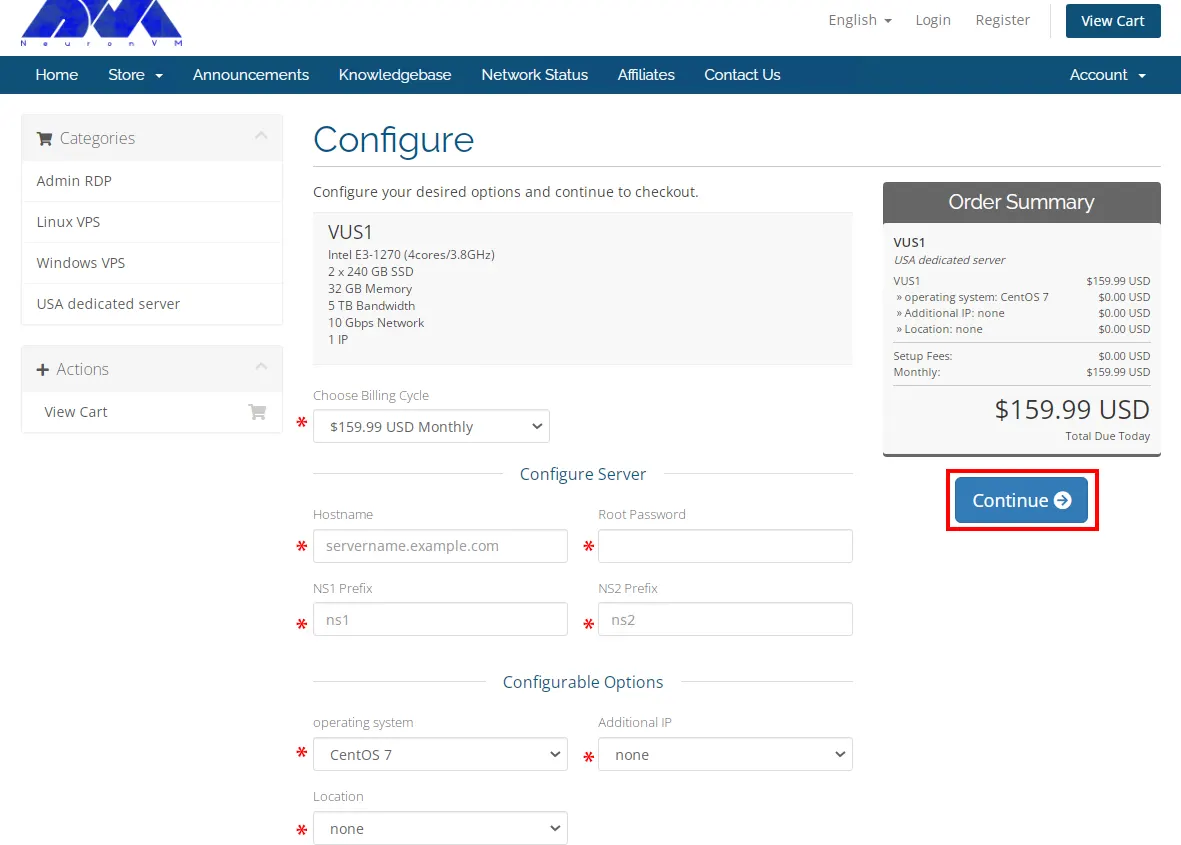
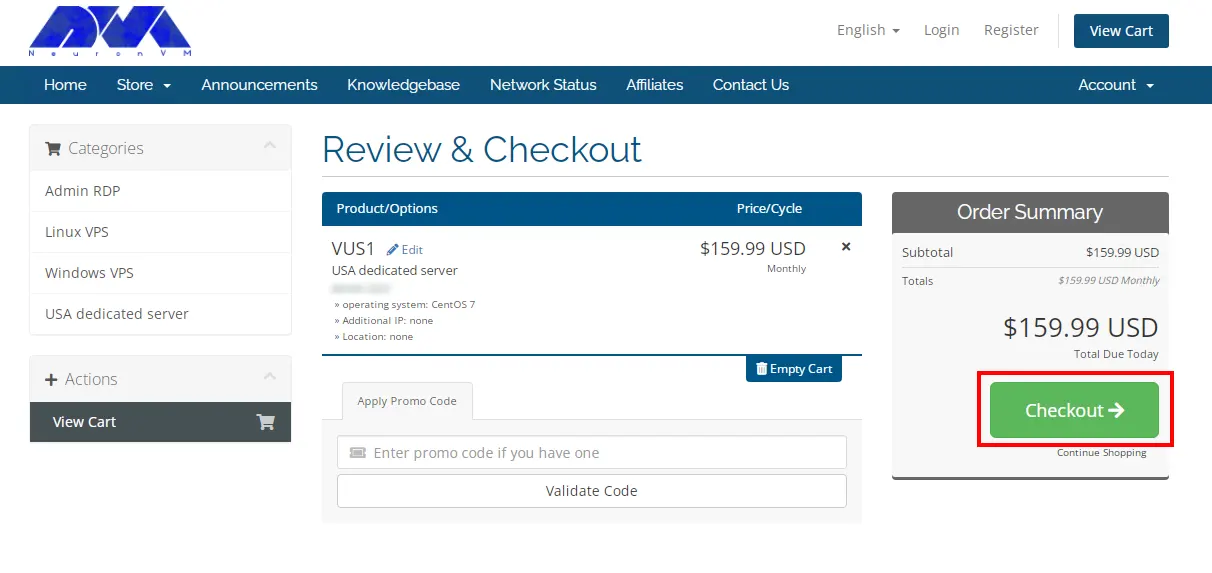
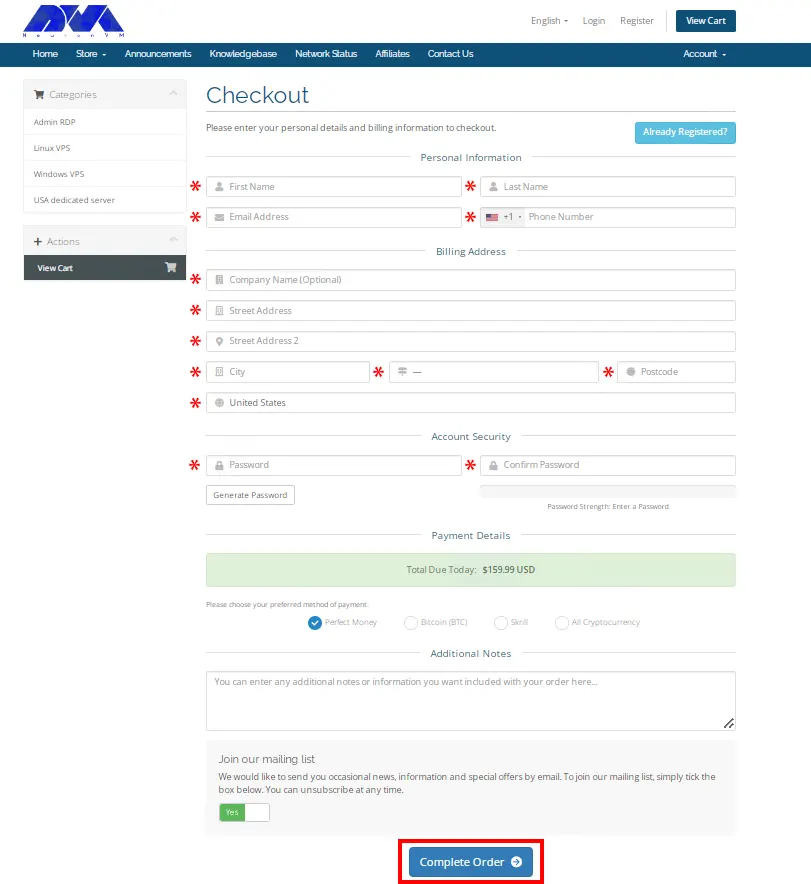
Note that to order a Linux VPS server, you can visit NeuronVM’s popular and cheap plans.
a- RedHat Linux open-source products include, but are not limited to:
b- RedHat Package Manager (RPM) program for installing, removing, and managing software in Linux.
c- RedHat Ansible is an open-source IT configuration management (CM) developer tool and IT automation platform.
d- RedHat Atomic Host is a variant of RedHat Enterprise Linux optimized for hosting containerized application platforms.
e- RedHat CloudForms is a virtual machine and container management product based on VMware, RedHat Virtualization, Microsoft Azure, OpenStack, AWS EC2, Google Cloud, and RedHat OpenShift.
f- RedHat Enterprise Linux (RHEL) is a Linux operating system distribution developed for the commercial market that provides centralized certificate management and cloud security updates.
g- RedHat’s OpenShift Container Platform is a cloud computing and microservice container platform used in conjunction with Kubernetes to provide traffic and identity management, telemetry, and policy enforcement.
h- RedHat Virtualization (RHV) is an enterprise-class virtualization platform.
i- RedHat Enterprise Linux environments, Satellite is part of RedHat’s four-piece system management tool suite for enterprise IT, which also includes Ansible, CloudForms, and the RedHat Insights service.
What are RedHat services?

Application services
1- RedHat fuse
2- RedHat Fuse Online
3- RedHat JBoss Enterprise Application Platform (JBoss EAP)
4- RedHat JBoss web server
5- RedHat AMQ
6- RedHat 3scale API Management
7- RedHat Data Network
8- RedHat CodeReady Studio
9- RedHat Decision Manager
10- RedHat Process Automation Manager
Cloud Computing
1- RedHat Certificate System
2- RedHat Directory Server
3- RedHat Quay
Data services
1- RedHat Gluster Storage
2- RedHat Ceph Storage
3- RedHat OpenShift Data Foundation
Management
1- RedHat Smart Management
2- RedHat Insights
3- RedHat Advanced Cluster Management for Kubernetes
4- RedHat Advanced Cluster Security for Kubernetes
RedHat Services
1- RedHat Open Innovation Labs
2- RedHat training and certification
3- RedHat Consulting
Data Services and Cloud Computing
– RedHat Hyperconverged Infrastructure (RHHI)
Advantages of choosing RedHat for Business
A large number of active Internet servers are currently supported by solutions developed by RedHat. In the public mind, the North Carolina-based organization is best known for its RedHat Enterprise Linux operating system.
Redhat Secure Design
RedHat and RedHat Enterprise Linux are widely recognized and admired for their highly secure engineering. Currently, this Linux distribution, which runs on IBM servers, has even reached the Common Criteria certification, the highest level of security certification in the world, which is allowed for use in government organizations. There are several reasons why the RedHat products have achieved such an advanced level of security.
Enterprise Linux does not require the use of third-party tools that can be dangerous to fix security flaws. It is also inherent in the transparency of open-source products, and the constant scrutiny they undergo from many independent parties makes it very difficult for malicious actors to create problems.
RedHat Open APIs
RedHat maintains a policy of providing open application programming interfaces and provides its customers with flexible tools to create the solutions they need. Open APIs also mean the freedom to build to your specifications.
RedHat Thorough Product Testing
RedHat has a policy of testing new hardware before entering the market. Currently, the company uses its various relationships with hardware manufacturers to ensure the performance of its products and those that have been available to consumers for years.
RedHat Cyber Security Quick Response
Currently, the RedHat security response team is actively tracking vulnerabilities to resolve them quickly. The team also has a track record of fixing more than 98% of critical vulnerabilities within a day of discovery, and the secret to this rapid response can be attributed to RedHat’s close working relationships with its partners, cybersecurity organizations, and the larger open source community. searched.
RedHat Legal Protection
RedHat’s open-source assurance program provides some important legal protections to its subscribers. Under this program, RedHat agrees to replace or modify the disputed portion of the Software while enabling Customer to continue using the Software without interruption. In addition, if another party sues for the alleged infringement, the customer will be provided with an attorney at RedHat’s expense.
RedHat Cutting-Edge Philosophy
RedHat has all the qualities to continue striving for innovation rather than settling for stagnation. The company maintains relationships with a large circle of hardware and software vendors, as well as a number of standard-setting industry organizations, ensuring that the company can respond quickly to technology and business trends. RedHat was a founding member and sponsor of the Advanced Message Queuing Protocol (AMQP) working group, which promotes this widely accepted open messaging protocol standard.
RedHat Scalability
When we talk about scalability, we refer to the capacity of a platform or application to handle increased operational needs without compromising its performance. A properly scalable platform is invaluable in our fast-moving technological society. A company can also easily experience a sudden increase in activity that it does not anticipate. Unless equipped for such a contingency, the system may be affected by this increase and have potentially harmful effects on the Company’s dealings with customers and vendors. RedHat Enterprise Linux is designed to provide maximum scalability to meet the fluid operational needs of the enterprise sector.
RedHat Support
RedHat’s technical support team is available 24/7 to provide the help and solutions you need to keep everything running smoothly. Currently, each of their support engineers holds a RedHat Certified Engineer certification or has years of relevant industry experience. You can also get the answer you need whenever you need it. In addition, RedHat has a policy of supporting its products not only around the clock but also over a long period of time and is committed to supporting the original versions of its software for up to ten years. It also guarantees full version compatibility.
RedHat Reasonable Cost
Currently, RedHat software and services operate on a subscription model, and the result is that it allows the company to avoid many support costs often associated with software hardware of this type. As a RedHat Subscription customer, you will not incur licensing, upgrade, or user access fees.
RedHat Flexible Subscription Options
RedHat gives its customers a lot of freedom with their subscriptions, which can be easily moved from one server to another, even from a physical server to a virtual server. Subscriptions are also not tied to any specific software version, thus giving customers more options in managing their workloads.
RedHat Effective Training Options
Any platform or app can be more trouble than it’s worth if the user can’t effectively use the training options. Also, in our fast-paced, high-tech world, it’s important to be able to find solutions immediately.
Conclusion
RedHat is an innovative open-source solution that anyone dealing with proper server operating systems or cloud applications will come across RedHat sooner or later. It identifies both the American software company and Linux distributions with the same name. RedHat symbolizes RedHat’s commitment as an agent in action for open-source in the digital world. In this Tutorial, you learned What is RedHat? We hope this article was useful for you.