The battle between Kali Linux and Arch Linux is a showdown between two powerhouses. Kali Linux, known for its penetration testing capabilities, is favored by cybersecurity professionals. Arch Linux, on the other hand, boasts a minimalistic approach and offers a highly customizable experience. In this article, you will clearly see the result of the comparison between Kali Linux vs Arch Linux.
The Origin Story
Kali Linux and Arch Linux are two popular Linux distributions that emerged from different origins and serve distinct purposes. Before we start and introduce and compare these two distributions for you, we suggest you to test and use the Linux VPS server plans provided on our website.
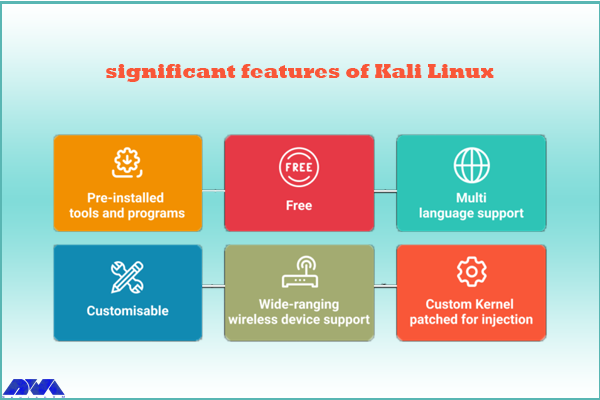
Kali Linux, formerly known as Backtrack, was initially developed by Mati Aharoni and Devon Kearns of Offensive Security as a specialized distribution for penetration testing and digital forensics. It was first released in 2006 and became popular within the security testing community due to its vast array of pre-installed security tools and utilities. Kali Linux is designed for ethical hacking and security auditing, providing a robust platform for professionals and enthusiasts in the cybersecurity field.
On the other hand, Arch Linux was created by Judd Vinet in 2002 as a minimalist and lightweight distribution focused on simplicity, customization, and flexibility. Arch Linux follows a rolling release model, which means that users have access to the latest software updates without the need for reinstalling the entire operating system. Its philosophy of “Keep It Simple, Stupid” (KISS) appeals to advanced Linux users who prefer to build their systems from the ground up and have complete control over every aspect of their installation.
Although Kali Linux and Arch Linux have different goals, they both share an open-source foundation and have vibrant communities supporting their development. Both distributions enjoy active user bases and periodically receive updates and bug fixes to ensure their security and functionality.
Kali Linux vs Arch Linux: Usability and User Experience
First of all, it should be noted that Kali Linux and Arch Linux both have different focuses, so their usability and user experience may vary.
Kali Linux comes pre-installed with a wide range of security and hacking tools, making it ideal for experienced security professionals. However, for a mainstream user who only requires general computing tasks, Kali Linux may not be the most user-friendly option. It requires a high level of technical knowledge and may not provide a seamless out-of-the-box experience.
On the other hand, Arch Linux is highly customizable distribution that follows a “do-it-yourself” philosophy. Arch Linux provides a more hands-on experience, allowing users to configure and optimize their system according to their specific needs. While this level of customizability can be empowering for experienced users, it may not be the best choice for beginners or those who prefer a more plug-and-play experience.

In terms of user experience, Kali Linux is focused on a specific niche and provides specialized tools for penetration testing and security assessments. Its user interface is tailored to these tasks, with an emphasis on efficiency and accessibility to security tools. However, for day-to-day tasks like web browsing, multimedia, or gaming, the user experience may not be as polished or optimized.
Arch Linux, on the other hand, provides a minimal and lightweight base system, allowing users to customize and install their preferred desktop environment, applications, and utilities. This flexibility offers a more tailored and user-friendly experience, but it also requires a higher degree of technical expertise to set up and maintain.
Package Management Systems
Kali Linux uses the Advanced Packaging Tool (APT) package management system. APT is known for its ease of use and powerful features. It allows users to install, upgrade, and remove software packages easily using simple commands like apt-get. APT also provides extensive dependency management, which ensures that all required libraries and dependencies are installed along with the requested package. Kali Linux also provides its own repositories with a wide range of security and hacking-related tools.
On the other hand, Arch Linux uses its own package manager called Pacman. Pacman is a lightweight and flexible package management system designed specifically for Arch Linux. It follows a minimalist approach and aims to provide a simple and efficient package installation process. Pacman uses a rolling release model, which means that packages are constantly updated to their latest versions. It also has a built-in package build system called the Arch Build System (ABS), which allows users to easily create and install custom packages.
In summary, both APT and Pacman have their own strengths and are suited for different types of users. APT is often preferred for its user-friendly interface and extensive package repositories, while Pacman is favored for its simplicity and rolling release model.
Community Support and Philosophies
Community Support:
Kali Linux: Kali Linux has a large and active community support base due to its popularity among the cybersecurity community. It has a dedicated forum, IRC channel, and various online communities where users can seek help, share knowledge, and discuss topics related to Kali Linux tools and usage.
Arch Linux: Arch Linux also has a strong and active community support system. It has an official forum, IRC channels, and a Wiki page. The Arch Linux community is known for its helpfulness, but it is more focused on user self-sufficiency and encourages users to find solutions on their own by providing extensive documentation.

Philosophies:
Kali Linux: Kali Linux is geared towards penetration testing, security auditing, and digital forensics. It is designed to provide a comprehensive toolkit of specialized tools for cybersecurity professionals. Kali Linux follows a philosophy of “hack responsibly” and promotes ethical hacking and education in the field of cybersecurity.
Arch Linux: Arch Linux follows a minimalist and do-it-yourself (DIY) philosophy. It aims to provide a lightweight and minimal base system that allows to build customized Linux environment according to preferences. Arch Linux focuses on simplicity, user-centricity, and providing the latest bleeding-edge software packages.
Kali Linux has a massive community support base with a focus on cybersecurity, hacking, and forensics, while Arch Linux has an active community that emphasizes self-sufficiency and encourages users to build their customized Linux systems. Choose Kali Linux if you specifically need cybersecurity tools, and choose Arch Linux if you prefer a minimal base system with extensive customization options.
General Overview: Kali Linux vs Arch Linux
In the table below, we have generally compared Kali Linux and Arch Linux. Note that this table provides an overview and may not cover all aspects of each distribution. It is always recommended to research and evaluate specific needs before choosing a Linux distribution.
| Features | Kali Linux | Arch Linux |
| Purpose | Penetration testing | Customizable environment |
| Target audience | Security professionals | Advanced Linux users |
| Ease of use | Intermediate | Advanced |
| Package manager | Apt | Pacman |
| Number of packages | Extensive | Minimal |
| Rolling release | No | Yes |
| Stability | Stable | Rolling release |
| Community support | Excellent | Active and knowledgeable |
| Documentation | Comprehensive | Extensive and detailed |
| Customization | Limited | Highly customizable |
| Hardware support | Wide range | Varies |
| Installation | Full installation image | Minimal installation image |
| Default desktop environment | Gnome | None |
| Security features | Extensive | Limited |
| Update frequency | Periodically | Continuously |
| Use cases | Penetration testing, digital forensics | General-purpose use |
Final Words
In conclusion, both Kali Linux and Arch Linux offer powerful features and flexibility for different purposes. Kali Linux is designed for penetration testing and security auditing, while Arch Linux is a minimalistic and customizable distribution suitable for advanced users. In this article, we tried to fully compare Kali Linux and Arch Linux, but if you still have any doubts or questions about this, ask us in the comments section.